The recognition of digital identity is not a purely technological issue; it has significant social repercussions, both on economic transactions and on individual lives. It is not necessary to identify the natural person who is, for example, making a digital payment, but it is necessary if one needs to assert their rights in the event of a dispute, such as in the case of an online scam. Current digital identification systems are effective at authenticating access to a computer system, but do not have the ability to easily attribute the real identity to the digital identity.
Digital identity recognition demands a holistic approach that takes into account the real world as well as the digital one. It requires the availability of a solution that offers convenient and secure identity management in the digital world while providing a demonstrable link to the true owner in the real world when needed. The transparency of management rules and the ease of use in identity processing are the main characteristics to facilitate the diffusion of such a solution.
Quality identity recognition systems in the digital environment should comprehensively satisfy the technological requirements for secure, practical use. The management of real identity is a highly structured organizational process. It is the result of complex international agreements to be able to act outside national borders but is strongly dependent on the laws of each individual country, which defines rules of release, use, and validity in its own territory. The digital world has no well-defined borders as access to the internet is generally open to all, but digital identity is valid only within the digital ecosystem to which it belongs. As its property, all identities in the specified ecosystem are unique.
The methods for managing the relationship between the two types of identities—real and digital—require refinement; they are not yet mature enough to guarantee trust in the ability to demonstrate this connection in a secure and simple, but also open and transparent, manner. Any solution to homogenize the identity management processes of the real and digital worlds, while maintaining the guarantees of security, ease of use, and independence of territorial authorities, makes any possible request for changes in the management of real identity to strengthen the equivalent in the digital world too complex, and therefore unrealistic.
The only way forward is to introduce a new solution on the digital side that can be used to strengthen information sharing between current digital identity management technologies and real identity organizational processes. To achieve this, it is useful to retrace the typical authentication mechanisms from an organizational, rather than a technological, perspective.
Typical Authentication Systems
The simplest system (and the oldest) is the conceptual model of the mainframe (figure 1), i.e., a central server in standalone mode that manages all client services without relying on the functionality of other servers. In this all-inclusive scheme, everything is managed within the system, from resources to users and all related controls. For the user, this means identity registration, authentication for access, authorization on data, and activity logs are in the same environment. The structure is very solid in terms of security, but the closed and rigid environment penalizes interoperability in a broader and more dynamic digital ecosystem.
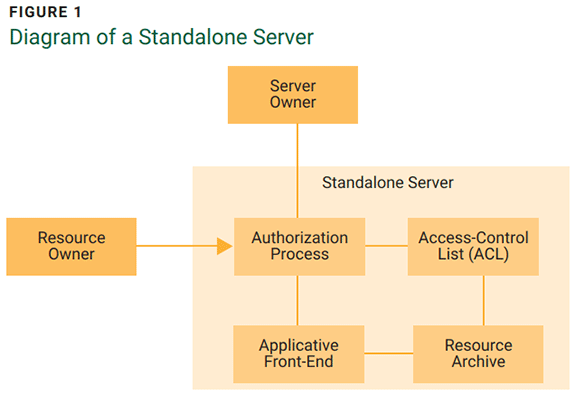
The server manages everything: user profiles, authorization process, and resources. The resource owner or user is the entity that requests the authorization process to access its resources. All users are defined in an access-control list (ACL) that determines for each user the operations allowed on certain resources. Access to resources is allowed only through application forms that filter the data of the various user operations.
More flexible is the internal authentication system of an organization with multiple servers that communicate to provide services. It is based on its own enterprise network domain defined by an authentication server dedicated to providing the authentication service to all entities in the domain (figure 2). The mechanism for accessing services is asymmetrical because only the client must be recognized, not the server that provides the services, because as a server it is always connected to the domain. Although it is possible to create trusted relationships between domains to obtain a more extensive network environment, the authentication system is owned by the organization that provides the services and directly manages the users registered in the domain.

One server manages user profiles and authorization process, and another manages resources; both are in the same domain. The resource owner has an application (user-agent) that manages the request for access to an online resource held by the resource server. The request is filtered by the relying party application (or website) that requests authentication to the authorization server. The authentication process is one-way because it concerns only the resource owner and not the relying party, which is already known to the authentication server as part of the domain.
As an extension of the concept of the enterprise network domain, the digital ecosystem (figure 3) considers all the functions present according to the concept of interoperable services, regardless of whether they are from the same organization. The authentication system itself is a service provided by a third party with respect to the user or supplier entities and represents the center of gravity on which the digital ecosystem is based. Compared to previous authentication schemas, it is designed to be open and manage services from different organizations for users who maintain the same credentials within the entire ecosystem. The authentication server manager is known as the identity provider and is independent of the service providers. Managing access credentials requires the registration of all entities in the ecosystem, both users and service providers.
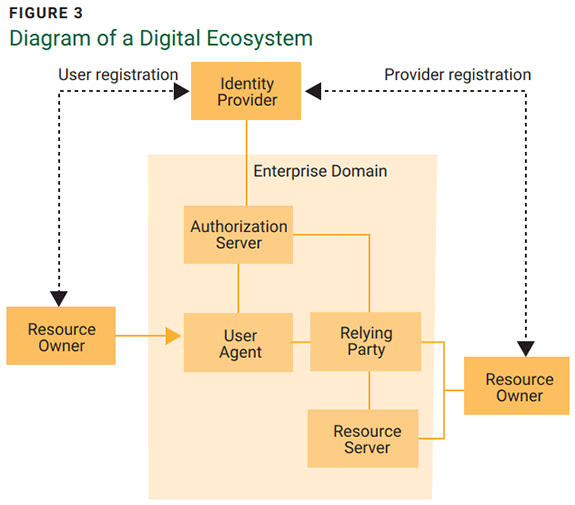
A third-party server manages the entity profiles and authorization process defining the ecosystem and another server manages the resources. The resource owner requests access to a resource that is not part of their organization, and the authorization server is managed by a third party that does not manage the resources. The owner of the resource server is the service provider, while the authorization server is the identity provider. Both the resource owner and the service provider must be registered by the identity provider in advance. It is the resource owner who must be recognized by the relying party (the service provider never authenticates itself for the user).
A digital ecosystem covers many of the needs of identity recognition, but two issues remain inadequately resolved: the extension of the authentication domain and the link between digital and real identity. The identity provider can federate its domain with other identity providers to create a larger ecosystem, but the extent of the internet is such that it can never be included in a single ecosystem, even if countless domains are federated. Consequently, a user must have at least as many credentials as there are ecosystems to which they need access. The second theme concerns the current authentication protocols that are designed not for the link between the digital and real worlds, but mainly for the effectiveness of authentication in the digital world. Instead, the approach used must be reviewed, also considering the possibility of needing to provide a guarantee of the real identity of the owner of the digital user.
Evolution of the Authentication Protocol
The main federated identity management models are Security Assertion Markup Language 2.0 (SAML2),1 which derives from the client-server paradigm with XML-based messages and OpenID Connect (OIDC),2 which, being more recent, prefers a standardized message exchange based on JSON and HTTP protocols. Both standards use, or are eligible to use, the OAuth 2.03 authentication framework, and for this reason it is currently the most widespread authentication protocol used in the creation of a digital ecosystem. OAuth 2.0 provides an open, simple, and secure authentication mechanism (figure 4).
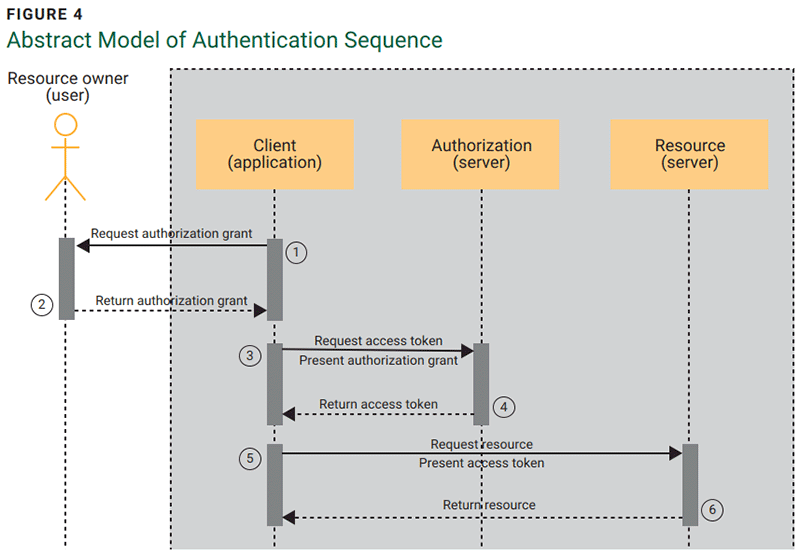
This authentication scheme requires the user to ask their user agent for access to a resource to which they have rights. The user agent is the application that receives the access request and manages all the phases of obtaining the digital resource. As an initial step, it asks the user for authentication credentials, then checks with the authorization server whether the credentials are valid, and finally, with the access token, requests and receives the desired resource. OAuth 2.0 provides an open, simple, and secure mechanism.
Despite these positive properties, there is an intrinsic limit to the digital ecosystem that is created with this authentication system. The authentication protocol is designed to authenticate only users of the domain (primary or federated) that contains the resources. To expand the user base, it is necessary to federate additional domains or request a new user registration for users who access resources on other domains not included in the authentication perimeter. It should also be noted that the authentication mechanism is asymmetric. This means that it is always the client who must be recognized by the service provider and not vice versa, i.e., there is no mutual recognition between the entity requesting the service and the provider. It can be compared to someone giving identity documents to a person wearing a uniform without wondering whether the person wearing the uniform has the authority to request them.
A symmetric authentication protocol4 can overcome this drawback. The symmetry derives from the principle that both entities must be recognized in a mirrored way (figure 5). Symmetry in the recognition cycle also strengthens security because it provides double verification on separate paths, hindering man in the middle (MitM)5 attacks.
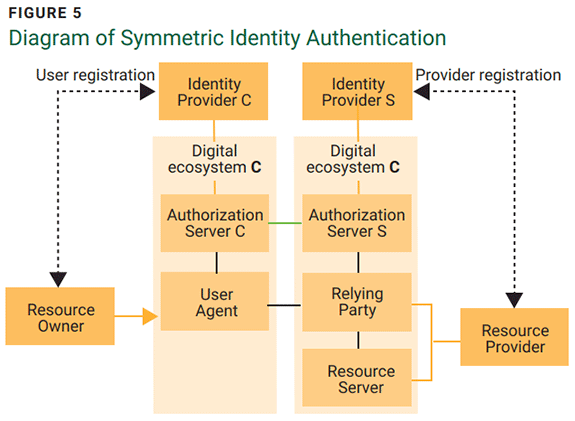
Each entity has a third-party server that manages the profile and authorization process defining the ecosystem that may include the resource server. The resource owner requests access to a resource that is not part of its domain, and the service provider will ensure that the identity is real by exchanging messages between the respective identity providers.6 The mechanism is based on the exchange of two-way authentication tokens between entities and between identity providers, but without domain federation. Token verification requires trusting the operations carried out by identity providers, but the trust must be deserved.
This mechanism does not require the user and the service provider to use the same domain. The identity authenticity verification is done for each entity by its own identity provider, which exchanges recognition verification messages with the other identity provider. Therefore, domain federation becomes unnecessary, but strict rules are required to ensure trust in the correctness of the identity provider’s operations and in the integrity of the message exchange. The current authentication protocol should not be replaced but adapted with the addition of the use case of out-of-domain symmetric authentication.
Digital identities allow only those with authority to proceed with real identification and allow users to receive protection for their rights, thus making economic transactions more reliable.The symmetric protocol can be an extension of the OAuth protocol, which, without replacing any functionality, should include a mechanism to allow the cross-exchange of out-of-domain messages to query the identity providers on the validity of the other identity or confirm one's own. The core of the token management mechanism is always the identity provider, which, due to the importance of the role it plays, must be independent from both the entities requesting services and those providing services,7 and their independence and reliability must be demonstrable. This presupposes a common code of conduct among all identity providers and a formal verification process in charge of international certification bodies to guarantee the correct functioning and robustness of the identity provider’s network. Verification should require a specific and prescriptively defined statement of applicability8 by the identity provider control authority.
Evolution of the Identity Provider
The identity provider, in providing the registration and recognition service of digital identities, must also guarantee a high degree of protection of the information of its entities. This means excluding a priori any further processing of the information of registered entities exceeding the needs of the service provided so as not to compromise the trust granted by the entities (e.g., avoiding behavioral profiling for marketing purposes). At the same time, to be a sustainable activity, a balanced registration cost and a subscription for the recognition activity must still be recognized. The organizational model must be oriented exclusively towards token authentication, because any collateral activity other than strengthening security undermines trust in this organization.
Transparency in operations is crucial for the credibility of the entire system. For this reason, to obtain an effective link between digital and real identity as well as a protection of the data of natural persons, it is necessary to divide the set of identity providers into two categories: custodians who manage the link between digital and real identity and trustees who manage identity in private or commercial transactions.9 The main differences between the two types of identity provider are:
- The custodian is governed by the same authority that manages the real identity and assigns a digital identity with full legal value. The main role is the custody, verification, and updating of the natural person's data, as well as managing the links with the digital identities issued by the trustees. For example, the custodian certifies the reliability of requests for the issuance of digital identities of individuals to trustees through an entirely digitized process.
- The trustee is a legal entity that only manages digital identity in online organizational transactions. It does not need to know the data of the natural person as it is guaranteed by the custodian and with several online formalities it allows the issuance, renaming, or deletion of digital identities used on the internet.
Having the authentication service in charge of a third party presents non-negligible considerations in terms of service performance, system resilience, and lower costs compared to an in-house process. An identity provider treats authentication as a core enterprise, which means guaranteeing a high quality of service always aligned with the current state of technology. Furthermore, in the management of the organizational continuity of the identity provider, the recovery point objective (RPO)10 parameter is not very significant because the integrity of the authentication message verification transaction requires that either the entire cycle is complete, or it is invalidated. A failed authentication cycle must be repeated and not restored to avoid vulnerabilities. Finally, requesting the service of an identity provider offers concrete organizational advantages:
- Avoiding the need to maintain a fixed internal structure with skill adjustments over time
- Having a guarantee of timely delivery of a given solution
- Tying the change to variable costs and not to the implementation of internal projects
- Transferring operational risk to a third party
Similarities Between the Digital and Real Worlds
When real identity crosses the borders of one's own country, a passport is required as a means of recognition. This document, based on international rules, both organizational and technical, allows one to have trust in the information it contains. Similarly, identities that come from outside the digital ecosystem require a formal mechanism to guarantee the integrity and plausibility of the recognizable information. The system that performs this function is the network of identity providers that must be based on continuous monitoring of compliance and periodic audit visits. The transparency of the governance rules of the identity provider’s network serves to promote overall trust in the system.
Applying formal rules of identity management and identity providers is not a limitation of freedom on the internet, but rather, it is an aid for a conscious use of technology. The resulting digital identities allow only those with authority to proceed with real identification and allow users to receive protection for their rights, thus making economic transactions more reliable. These digital identities, even real (DIER) bring a dichotomy to the internet. Which type of identity to use is a choice.
Conclusion
The management of digital identity recognition and its link to real identity must be addressed holistically, both from a technological and civil perspective. In the digital world, symmetric authentication serves as an example of an authentication protocol that can overcome the limit of domain federation. In the real world, identity providers that satisfy local laws and technology requirements build trust in the organization and the entities that manage identities for them. The use of an authentication protocol based on message authentication rather than domain federation has the right characteristics to create the technological foundation for the digital identity recognition system.
In short, current methods of managing real identity should not change. The identity provider's organizational model must be based on rules of independence from service providers and protection of identity data confidentiality to ensure market trust in the service offered and improve its diffusion at a global level. An appropriate international authority must have the ability to decide on the behavior and disabling of identity providers through a system of checks and balances to guarantee the legitimate functioning of identity providers. This is a necessary condition to gain the trust of users and guarantee the ability to carry out legal user tracking.
Current identity providers are tied to the need to facilitate the use of a pool of services with a single ID (i.e., single sign-on). It is a limited vision that does not go beyond the single digital ecosystem and makes the role of the identity provider too immature to be well recognized by the market. The areas where the identity recognition management process needs improvement are the digital identity linked to the real identity, the authentication mechanism independent of the ecosystem of belonging, and the protection of the rights of the person. The success of the entire process is based on two expectations: It must be simple and reliable.
Endnotes
1 OAuth, “OAuth 2.0”
2 OpenID, “What Is OpenID Connect”
3 OAuth, “OAuth 2.0”
4 Sbriz, L.; “A Symmetrical Framework for the Exchange of Identity Credentials Based on the Trust Paradigm, Part 1 & 2,” ISACA® Journal, vol. 2, 2022
5 ISACA®, “Man-in-the-Middle Attack (MitM)”
6 Internet Engineering Task Force, “Internet-Draft - Identity Trust System,” November 2024
7 Sbriz, L.; “How to Digitally Verify Human Identity: The Case of Voting,” ISACA Journal, vol. 1, 2023
8 International Organization for Standardization (ISO), ISO/IEC 27001:2022 Information Security, Cybersecurity and Privacy Protection—Information Security Management Systems—Requirements, 2022
9 Sbriz, L.; “Modeling an Identity Trust System,” ISACA Journal, vol. 6, 2023
10 ISACA, “Recovery Point Objective (RPO)”
LUIGI SBRIZ | CISM, CRISC, CDPSE, ISO/IEC 27001 L A, ITIL V4, NIST CSF, TISAX AL3, UNI 11697:2017 DPO
Is a lead auditor, trainer, and senior consultant on risk management, cybersecurity, and privacy issues and has been the risk monitoring manager at a multinational automotive company for more than seven years. Previously, he was head of ICT's operations and resources in the APAC region (China, Japan, and Malaysia) after serving as worldwide information security officer for more than seven years. He developed an original methodology for risk monitoring, integrating operational risk analysis tools, a control maturity assessment, and a risk-based internal audit process. Additionally, he designed an OSINT-based cyber monitoring tool and is proposing a digital identity authentication standard. Sbriz was a consultant for business intelligence systems for several years. He can be contacted on LinkedIn.
