Somewhere a trusted employee, embedded within the core of an institution, is secretly siphoning off resources for personal gain. Occupational fraud is an unfortunate reality. This form of fraud involves the misuse of enterprise resources and poses unique challenges distinct from other risk, primarily due to its purely negative impact: causing financial and reputational damage without any potential upside.
Relying on traditional risk management strategies to address such fraud is far from ideal, due to the ability of insider fraudsters to adapt swiftly to countermeasures. This necessitates a proactive approach to fraud prevention that leverages emerging technologies to unveil the nuanced traces of potential fraudsters. This approach can be integrated with domain expertise to achieve more effective and continuous identification of fraud.
Why Occupational Fraud Matters to Digital Banks
The rise of digital banks has transformed access to financial services for underserved customers. Unlike conventional banks, digital banks operate with a much leaner organizational structure and without a branch network. Although their customer-facing processes may be primarily digital, these banks are still supported by various back-end business and management processes, each with a different level of digital maturity. The shift toward digitalization has exposed banks to new vulnerabilities regarding occupational fraud, particularly in areas of customer acquisition, third-party relationships, and human intervention (i.e., keeping a “human in the loop”).
Customer Acquisition
While most digital banks primarily use digital marketing channels, they still incorporate traditional marketing methods such as telemarketing to some extent. For example, in digital lending to small businesses, telemarketing staff can help prospective customers complete credit applications and encourage referrals from existing clients. Similar to customer relationship managers at bank branches, telemarketers can maintain direct relationships with customers through calls or messages, with a focus on high-value clients. However, these close connections may lead to insider abuse, such as the sharing of valuable customer information withcompetitors.
Third-Party Relationships
As new entrants to the industry, many digital banks have partnered with nonfinancial internet platforms for customer acquisition and servicing—for example, to offer buy-now-pay-later (BNPL) options on e-commerce websites. These agreements are negotiated on a case-by-case basis to ensure seamless integration between the digital banks and third-party platforms, with dedicated teams within the banks fostering strong partner relationships. However, these arrangements can also open the door to potential insider fraud. For example, digital banks usually pay third-party platforms for customer referrals, but the customized nature of these agreements often means there is a lack of comparable market data to determine the fair level of referral fees. Sometimes this important matter is left to the discretion of the relationship teams and third parties, who might be tempted to agree on unfair fees for personal gain.
Keeping a Human in the Loop
In digital banks, many customer-facing decisions (e.g., credit underwriting) are now intelligently automated. However, on the back end, human involvement still plays a significant role. For instance, risk managers are responsible for continuously monitoring and refining the credit standards and criteria for automated underwriting decisions. This human-in-the-loop approach applies checks and balances to automated decision making, but it can also expose critical elements of automated decisions to human manipulation.
Detecting Fraud Perpetrators: From Red Flags to Social Network Analysis
The challenges of occupational fraud in digital banks necessitate innovative approaches to assess fraud risk and detect fraudulent cues. Ideally, such approaches should:- Harness the diverse data collected in daily operations for continuous fraud detection.
- Leverage industry-leading research on common characteristics of fraud perpetrators.
- Apply exploratory analytics to uncover fraud cues beyond human expertise.
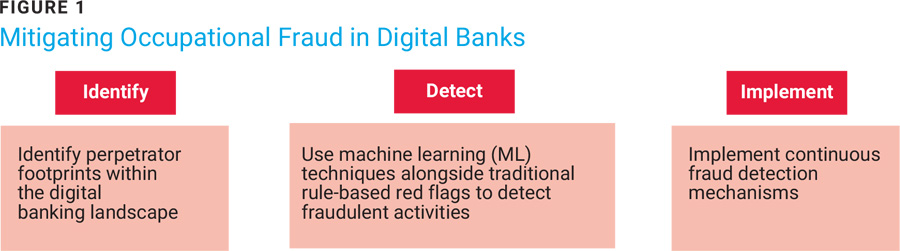
Consequently, a three-step process is proposed in figure 1.
Perpetrator Footprinting
Footprinting involves gathering information about potential perpetrators—specifically, employees likely to commit fraud—and the clues they provide. This task is challenging, as organizations may have few or no identified fraud cases to study for insights. However, industry-leading research can provide valuable insights. The Association of Certified Fraud Examiners (ACFE), for example, has identified key behavioral red flags of occupational fraud.1 The example in figure 2 shows the top three red flags from ACFE’s list to help determine which business processes could reveal such perpetrators and the specific rules that would raise red flags in this context.
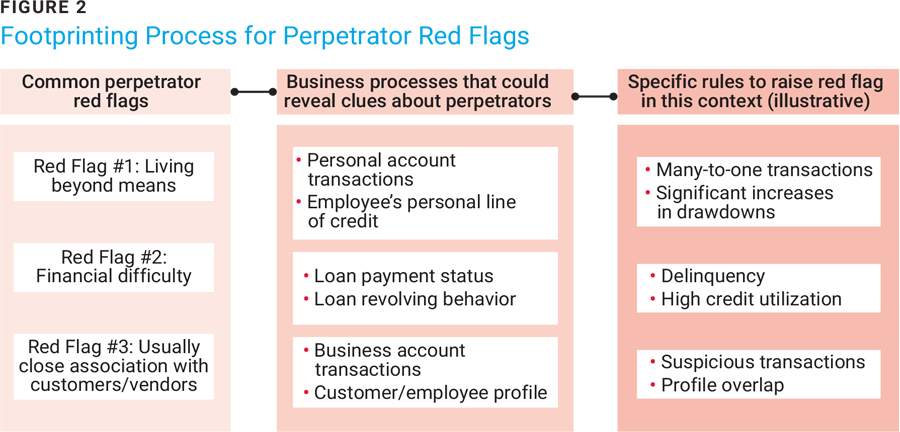
Red Flag #1: Living Beyond Means
Suspect personal account transactions include sudden, substantial fund transfers from multiple employees to a single employee. Accounts opened in digital banks may be used by employees to send or receive funds needed to support an excessive lifestyle. Similarly, an employee’s personal line of credit extended by digital banks may be utilized to fund lavish expenses.
Red Flag #2: Financial Difficulty
Loan payment status can be telling. Consecutive loan repayment delinquencies by employees on personal loans could provide early signs of financial difficulty. Likewise, loan revolving behavior exhibited by an employee persistently opting for minimum monthly payments could indicate financial trouble.
Red Flag #3: Unusually Close Association With Customers/Vendors
Business account transactions, when funds are transferred between business accounts of the bank’s partners/vendors and accounts controlled by the bank’s employees, should be monitored for suspicious activity. Customer and employee profiles with overlapping contact information (e.g., phone numbers, email addresses, physical addresses) that cannot be explained may be unreported for nefarious purposes.
Perpetrator Network Analysis
According to the ACFE, more than half (54%) of occupational fraud acts were carried out by multiple perpetrators rather than single individuals.2 While red flags are early signs of fraud detection, they can sometimes be limited in identifying colluding fraudsters. This is where social network analysis can play a bigger role. In this context, it typically involves centrality analysis and network discovery.
Centrality Analysis
Centrality measures the influence of a node (e.g., an employee) within a network (e.g., connections between employees and customers). One such measure is degree centrality, which counts a node's direct connections, indicating how well-connected it is. Network centrality analysis can reveal potential issues, as higher influence may suggest unusually close relationships. In figure 3, which illustrates the case of telemarketing staff engaging customers and seeking referrals, nodes with high centrality can be identified as:
- High centrality customers—Customers who refer significantly more prospects to a single telemarketer than the average customer. The underlying risk: These customers may be unauthorized loan brokers in disguise.
- High centrality telemarketers—Telemarketers with a higher percentage of referrals from high centrality customers compared to their peers. The underlying risk: This situation raises the possibility of collusion between telemarketers and loan brokers in disguise (the high centrality customers).
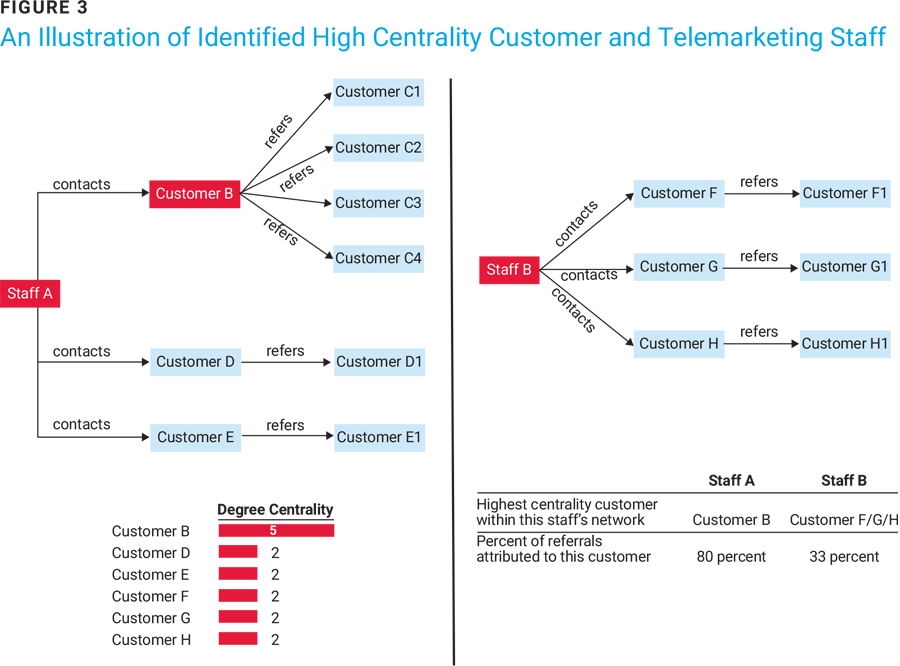
In this example, Cust B is identified as the high centrality customer due to having a higher degree of centrality than other customers. Telemarketing Staff A is identified as the high centrality telemarketer due to having more referrals related to a single customer (Cust B).
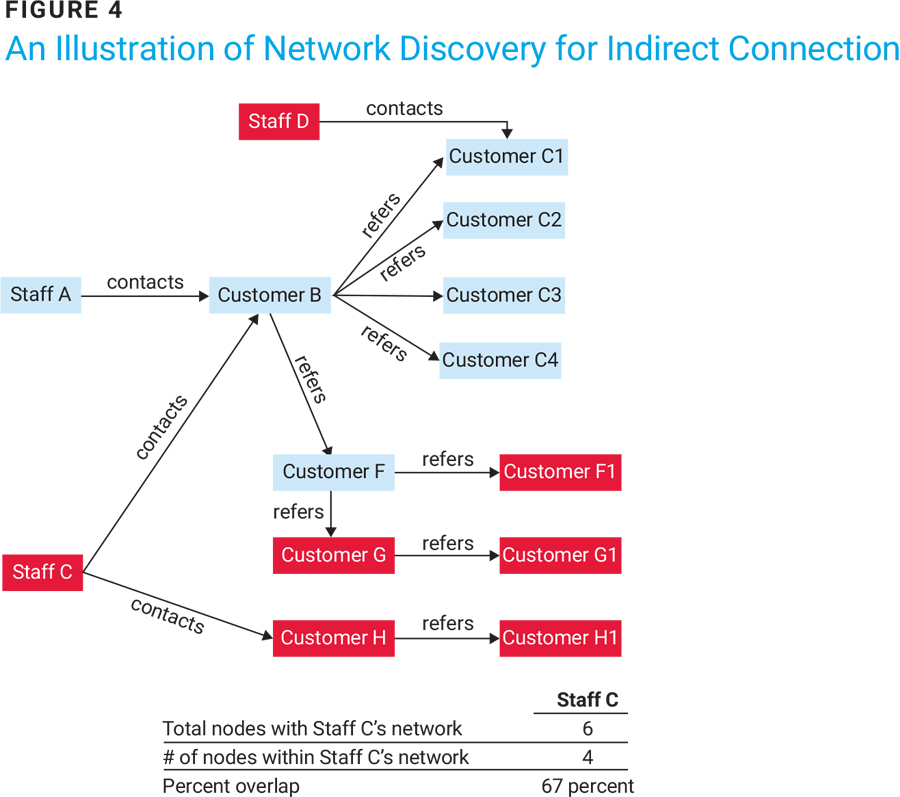
Network Discovery for Indirect Connections
High centrality nodes may represent merely the tip of the iceberg in a collusive fraud scheme. It is important to identify other nodes that may be indirectly connected to the high centrality nodes that could be part of a colluding group.
In the context of telemarketing customer relationships, if a high centrality customer is suspected of being an unauthorized loan broker in disguise, further investigation is warranted to determine whether other telemarketing staff are colluding with the broker in less subtle ways. This can be achieved by exploring all direct and indirect connections to the high centrality customer, such as referrals of referrals, to identify overlapping referral networks among different telemarketers. While some overlap may be coincidental, a significant level of overlap raises concerns. The degree of overlap can be measured by examining the percentage of a telemarketer's network that consists of nodes (i.e., customers) also found in other telemarketers' networks.
Figure 4 illustrates an example of network discovery to identify a group of telemarketers colluding with loan brokers disguised as the bank’s customers. In this example, although Cust B is clearly a high centrality customer within telemarketing Staff A’s network, Cust B’s direct and indirect referrals (F/F1/G/G1) also make up two-thirds of telemarketing Staff C’s network, indicating the likelihood that Staff C might be colluding with Cust B (a loan broker) in addition to Staff A.
Implement Continuous Fraud Monitoring
Occupational fraud often can go undetected for extended periods, with longer durations leading to greater losses. Therefore, organizations must proactively undertake continuous efforts to detect and minimize fraud. Implementing continuous fraud monitoring hinges on three key questions aimed at building the supporting infrastructure:
- What data is available on a continuous basis to support fraud detection?
- What best-of-breed analytic tools and algorithms can be accessed conveniently?
- Once fraud cues are identified, how will they be investigated?
Data Availability
Continuous fraud monitoring is a prerequisite for access to:
- Master data elements—Profiles of the bank’s employees, vendors/partners, and customers include contact information, bank account numbers dependents, family members, and significantcontrollers.
- Transactionand relationship data—This encompasses fund transfer transactions, telemarketing staff assignments to customers, and customer referral relationships.
Overall, harnessing the full potential of relationship data serves as the secret weapon for effectively identifying colluding perpetrators.
Analytic Tools
The advancement of artificial intelligence and ML has introduced a variety of algorithms and analytic techniques to support fraud monitoring. One such example is graph technology, which focuses on understanding and analyzing the relationships between different data points. In simple terms, graph technology uses a structure made up of nodes (which represent entities such as customers or staff) and edges (which represent the connections between the entities). This approach allows for in-depth analysis of networks, making it easier to uncover unusual relationships that could indicate insider fraud.
Follow-Up Steps
Continuous fraud monitoring requires a robust governance structure. Senior management and the board ensure that several key steps are taken:
- Oversee—Provide oversight for fraud monitoring programs and handle the escalation of fraud issues or implementation of corrective actions.
- Align—Ensure that the objectives and priorities of fraud monitoring programs align with the bank’s risk appetite, considering the rapidly changing digital banking environment.
- Investigate—Emphasize root cause analysis and corrective action recommendations during fraud investigations, adapting industry practices to the unique challenges of digital banks.
- Implement—Implement corrective actions through cross-functional collaboration. For recently established digital banks, adjust organizational roles and responsibilities based on lessons learned to ensure the effectiveness of preventive controls.
Conclusion
Digitalization impacts not only customer-facing processes but also back-end functions, such as managing the risk of occupational fraud in digital banks. It creates new vulnerabilities in various business areas while simultaneously providing a wealth of data and technologies to monitor fraud indicators and reduce associated costs. Effective fraud monitoring in digital banks requires strong leadership, management support, and a commitment to continuous improvement, all while adapting to the constantly evolving landscape of fraud.
Endnotes
1 Association of Certified Fraud Examiners, Occupational Fraud 2024: A Report to the Nations2 Association of Certified Fraud Examiners, Occupational Fraud 2024
TERRENCE CAI | CISA, CIA, CISSP, FRM
Is an internal auditor at a digital-only bank in China. He oversees continuous auditing solutions and audit analytics for the bank’s lending business, including consumer and small business lending.
