As cyberthreats continue to evolve in sophistication, attackers are increasingly employing advanced techniques such as fileless malware, artificial intelligence (AI)-powered phishing campaigns, and living-off-the-land (LotL) tactics to evade traditional security measures. Fileless malware operates directly within a system's memory, leaving minimal traces and making detection challenging. AI-powered phishing crafts highly personalized and convincing fraudulent messages, enhancing the likelihood of successful breaches. LotL tactics involve the misuse of legitimate system tools and processes, allowing malicious activities to blend seamlessly with normal operations. These evolving threats demand adaptive security strategies that incorporate behavioral analysis, threat intelligence, and proactive monitoring.
Organizations relying on standard security tools may miss sophisticated APT techniques unless they implement specialized threat intelligence and proactive monitoring strategies.Organizations must develop advanced strategies to detect and counter these advanced persistent threats (APTs). Most security tools scan for indicators of APTs, but their effectiveness varies. Traditional antivirus and endpoint detection systems primarily focus on known signatures and behavioral anomalies, which may not always detect the stealthy persistence mechanisms used by APTs. More advanced security solutions, such as extended detection and response (XDR) platforms and threat hunting tools, are specifically designed to analyze deep system behaviors, registry changes, scheduled tasks, and fileless malware tactics. Organizations relying on standard security tools may miss sophisticated APT techniques unless they implement specialized threat intelligence and proactive monitoring strategies.
There are several common techniques employed by APT groups to achieve persistence, such as the use of batch scripts, registry modifications, and backdoor deployments. By analyzing these tactics, threat hunters can gain a deeper understanding of the attack vectors commonly exploited by APTs. This, in turn, helps enhance their ability to detect and respond to persistent threats effectively.
Batch Script Execution Tactics
Attackers commonly use batch scripts in APT attacks for several practical reasons. One reason is that these scripts are easy to write and execute, making them a convenient tool for attackers. Since batch files do not require compiling or specialized software, they enable attackers to quickly automate tasks such as file manipulation, command execution, and system configuration changes. Batch scripts can be run directly from the command line, allowing attackers to perform various actions without relying on complex tools or code.
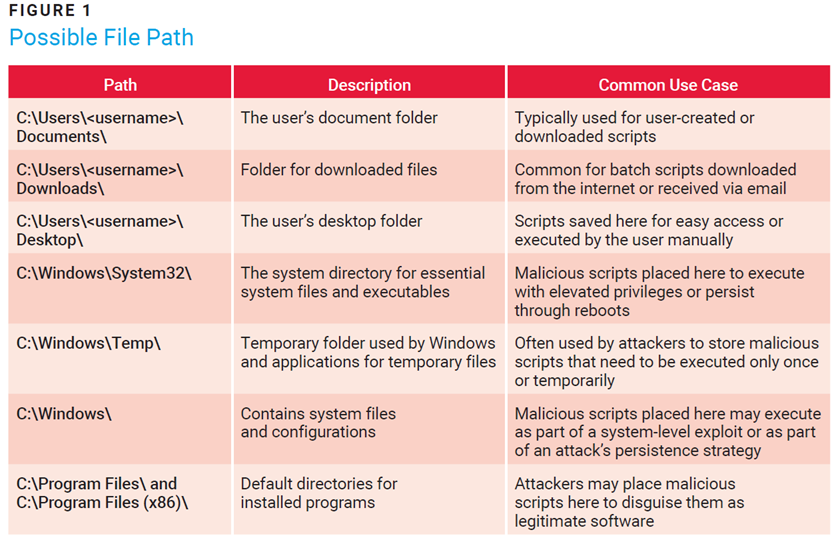
The possible use of cmd.exe to execute commands for listing extension (.bat) files with specific keywords may indicate an attempt to establish long-term access or control over the system. The presence of such a file in any folder (figure 1), along with a suspicious batch script, could suggest the involvement of a potentially malicious program. This could be related to a variety of attack tools or simply be the initial stage of adversarial activity aimed at gaining a foothold on the system.
Such behavior is commonly seen when attackers try to ensure access even after reboots or other security measures are applied. The use of unusual scripts or tools in this context often signals the early phases of an attack when the intruder is preparing for further exploitation or securing continued access to the system.
One of the main reasons attackers use batch scripts is to establish persistence. They modify system settings, add entries to startup folders, or manipulate the Task Scheduler and registry keys to ensure that malicious processes are executed every time the system restarts. This method enables attackers to maintain access to the compromised system over an extended period, even after reboots or user logins. By using batch scripts to automatically launch malicious payloads, attackers can ensure long-term control of the system, a characteristic of APT attacks.
Task Scheduling and Credential Dumping Tactics
In an APT attack scenario, the attacker will likely use at.exe, a command-line utility in Windows, to schedule a task that could run a tool such as Mimikatz1 to harvest sensitive login credentials from the compromised system. This tactic enables the attacker to silently collect authentication data while minimizing the chances of immediate detection. By scheduling the execution of such a tool, typically used to extract credentials from system memory, the attacker ensures that the malicious action can occur at a specified time, without requiring user interaction. This approach makes it more difficult for traditional security tools to detect the attack in real time, as the tool may run unnoticed in the background.
The attacker can also place the malicious files in a folder typically used for storing downloaded files, allowing them to blend in with normal user activity. The files involved may be part of a larger malicious toolset often associated with penetration testing or APT operations, aimed at exploiting vulnerabilities and establishing long-term access to the system.
Scheduling the execution of a credential-dumping tool such as Mimikatz via at.exe enables the attacker to gather credentials over time, remaining stealthy and minimizing detection. This method is commonly seen in advanced cyberattacks. In the 2017 NotPetya ransomware attack, attackers utilized Mimikatz to extract credentials from infected systems, facilitating lateral movement across networks. By scheduling the execution of Mimikatz, they maintained prolonged access while minimizing detection. This method exemplifies the sophisticated techniques employed in advanced cyberattacks.2
Registry Modification
In APT attacks, attackers may use reg.exe, a legitimate Windows utility, to modify the registry and establish a backdoor or create additional user accounts for persistent access. By targeting critical registry keys, such as those used for startup programs, attackers can add entries and ensure that their malicious software or scripts execute automatically whenever the system restarts.
Through commands such as reg add, attackers may also configure the registry to launch a backdoor executable, connect to a remote server, or even create a new user account with elevated privileges. Adding a new user gives the attacker a secondary method to access the system, which can be useful if the original backdoor is detected or removed. This tactic allows attackers to maintain control over the system, exfiltrate sensitive data, or escalate privileges while avoiding detection. Using reg.exe to automate these actions provides attackers with stealth and persistence, enabling them to infiltrate the target environment over extended periods.
APT Risk: A Review
In ATP attacks, attackers gain elevated access to systems, potentially enabling full control of the environment, sensitive data exposure, and further compromise of connected systems. There are several ways attackers can establish control over a system:
- The establishment of backdoors or the creation of additional user accounts ensures that attackers maintain access over an extended period of time, even after the system reboots or attempts to clean the system.
- Credential theft tools such as Mimikatz allow attackers to harvest sensitive login credentials, leading to further lateral movement, unauthorized access to other systems, and potential data theft.
- Attackers can use modified registry keys to deploy malware or backdoors. This allows for the possibility of future attacks, remote control of systems, or the spread of ransomware.
- By maintaining access or introducing malicious processes, attackers can disrupt business continuity, cause downtime, or sabotage critical operations.
- The use of legitimate system utilities such as reg. exe and task scheduling tools such as at.exe to execute malicious code helps attackers blend in with normal system operations, evading detection by traditional security tools.
- Attackers can exfiltrate sensitive data, compromising confidential business or customer information and leading to financial, reputational, or regulatory damage.
Recommendations
If an enterprise fails to implement certain tools, attackers can operate undetected, leveraging advanced tactics such as credential dumping, lateral movement, and stealthy persistence mechanisms. Such a lack of visibility can lead to prolonged data breaches, financial losses, regulatory penalties, and reputational damage. Implementing several vital security measures is crucial to identifying, analyzing, and mitigating threats before they escalate into full-scale cyberincidents:
- Install Sysmon3 or an enhanced logging and monitoring software (e.g., an endpoint protection platform [EPP], EDR) to enhance logging capabilities, enable detailed event logging, and monitor system activity.
- Enable 24/7 monitoring of logs to track system events and detect any potential malicious activity.
- Track unauthorized modifications to registry keys, particularly Run keys, and set alerts for suspicious entries.
- Log and audit the use of reg.exe, cmd.exe, and PowerShell to detect suspicious command executions.
- Create alerts for new user account creation or privilege escalation, especially with administrative rights.
- Monitor the use of at.exe and schtasks for any task scheduling that runs unauthorized executables or scripts.
- Use application control to block unapproved executables and allow only trusted software to run.
- Perform periodic reviews of system logs, user activity, and configuration changes to detect anomalies.
- Look for batch files (.bat) at unknown or suspicious paths and monitor their associated processes.
Conclusion
As cyberthreats continue to evolve, the techniques employed by APT groups become increasingly sophisticated, making it essential for organizations to adapt and strengthen their detection and response capabilities. The use of tactics such as batch scripts, registry modifications, task scheduling, and credential dumping allows attackers to establish persistence, maintain control over compromised systems, and stealthily exfiltrate sensitive data. By understanding common methods utilized by attackers, security professionals can better identify potential attack vectors and enhance their ability to defend against APTs.
To mitigate the risk associated with these attacks, it is crucial to implement comprehensive monitoring solutions and enforce strict access controls to detect malicious activity early. Regularly auditing system logs, monitoring unauthorized changes to critical system configurations, and tracking the use of command-line utilities such as reg.exe, cmd.exe, and at.exe can provide valuable insights into the health of the system and potential threats.
Ultimately, proactive security measures, continuous monitoring, and an understanding of the common tactics used by attackers will greatly enhance an organization’s ability to detect, respond to, and recover from APTs, ensuring the integrity and security of their systems over time.
Endnotes
1 Mulder, J.; Mimikatz Overview, Defenses and Detection, SANS, 29 February 2016
2 Heinemeyer, M.; “Catching Mimikatz Behavior With Anomaly Detection Defense,” Darktrace, 14 February 2019
3 Microsoft Learn, “Sysmon v15.15,” 23 July 2024
HRISHITVA PATEL
Is a dedicated professional with a profound passion for technology, data analytics, and art. Currently pursuing a Ph.D. in information systems at the University of Texas at San Antonio (USA), Patel explores the frontiers of data-driven decision making. Beyond academic and professional pursuits, he finds creative expression through painting, balancing innovation with artistic passion.