



Organizations often approach Industrial Control System/Operational Technology (ICS/OT) cybersecurity as though cyberthreats are visibly evident and instantly recognizable, but today’s reality is different. The battleground has changed.
The Challenge
Modern malware is smarter than ever — it patiently hides, observes and strikes when the moment is right. This exposes an issue with timely decision-making. When we look at the traditional ICS/ OT cybersecurity, it's mapped out, roughly, like this:
Malicious activity occurs → Alert is fired →
Security team investigates → Decision is made

This model collapses when a smart malware adapts and blends with the normal operations. It acts only when security teams are least likely to take notice or detect the malicious activity – for example, during shift changes, maintenance work or peak production.
AI-Native Malware
Most ICS/OT defense systems are designed to be reactive, which is blind to threats that think ahead. The arrival of AI-native malwares such as DeepLocker and LameHug have introduced all-time-high stealthy mechanisms and traditional anti-malware are effectively useless against these polymorphic threats. These AI-native malwares normally possess the following properties:
- Learn and blend into the normal operations
- Adapt to the evolving detection techniques
- Change their state/behavior as needed
- Camouflage in the legitimate applications
- Hide the target identification and trigger logic using Deep Neural Networks (DNNs)
These attributes make the AI-native malwares stronger than ever.
Outmoded Governance
When selecting cybersecurity tools, traditional leadership is usually concerned about whether a system can detect threats or meet compliance requirements, whereas the concerning aspects should be the timeliness of detection, required actions, responsiveness and recoverability — most importantly, what risks it accumulates and what is the operational impact during any delay of detection and action?
This gap is exactly where the smart AI-native malwares operate. These malwares do not shut down the system completely or trigger alarms, but instead make small, subtle changes to the timing, sequencing, or process behavior. Those adjustments create risks, and teams only take notice once the impact has already happened.
The role of artificial intelligence in ICS/ OT is all about the anticipation and predictabilityof threats rather than detection and response. When AI is governed properly, it can learn the normal process behavior and notice small deviations that would never trigger traditional alarms. This matters because in industrial environments, timing and sequencing are as important as commands themselves.
Let's imagine a chemical plant where malware slips through a phishing email to maintenance software. The AI system will detect changes, such as the delays in valve timing that may hint at an attack. The AI will predict the next step and alert the teams.
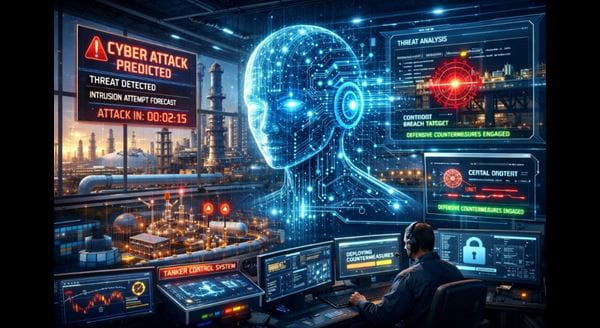
AI Predictability of Cyberattacks
AI use is a governance decision. A visionary and adaptive leadership identifies who owns the risk decisions, under what conditions AI is permitted to act autonomously and how the effectiveness of these controls will be measured.
Without clear decision authority and accountability, AI becomes another tool generating insights without an action plan. In industrial environments, the absence of forward-thinking security governance can be as dangerous as the absence of detection itself.
It is important to ask questions like how do we make sure AI works safely and reliably? The risk lies in doing nothing while smart malware waits.
Preliminary Conceptual Suggestions
While promising, widespread adoption of AI-powered ICS/OT cybersecurity is in its early stages, requiring deeper integration and proven reliability. Following are a few preliminary conceptual suggestions to begin the journey:
- AI-powered behavioral analysis: Use deep learning to predict anomalies.
- Identifying “AI within AI” indicators: Identifying any non-legit AI aspects.
- Deception technology: Use of machine learning-powered Honeypots.
- Explainable AI (XAI): Use of XAI methods to understand the adversarial context.
Predictive Defense is Critical
The cybersecurity landscape has changed where smart malwares work quietly, understanding the ICS/OT processes better than any system or human being, and launch cyberattacks that may go unnoticed by any detection tools. Integrating AI into ICS/OT for predictive cyberattack defense isn't just beneficial; it's a critical governance decision to ensure operational resilience against evolving threats.
