There is a dire need for workers with marketable security skills, from traditional information security to modern cybersecurity. The notion of a gap in the availability of skilled workers is not novel, although there are differing opinions on the gravity of the situation and a fair amount of ink spilled on ways to close the perceived gap. Economic uncertainty influencing employer hiring practices,1 a shortage of entry-level positions,2 and an unverifiable number of openings3 compound matters. Reports from the World Economic Forum (WEF), ISACA®, and the Associated Press paint a grim picture of the future of cybersecurity:
- In 2023, of the 40,000 cybersecurity jobs available in India, 30% went unfilled. Further, only 20,000 of Africa’s 1.4 billion people had cybersecurity certifications. Additionally, in the United Kingdom, 43% of small and medium-sized businesses (SMBs) had cybersecurity vacancies.4
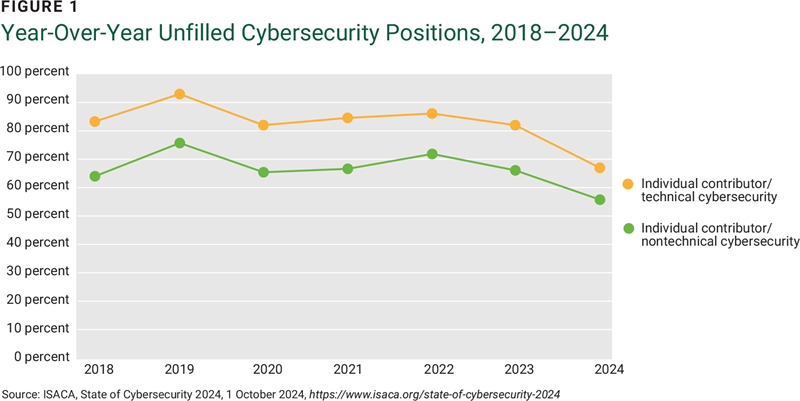
- In 2024, 68% of respondents to an ISACA survey had unfilled entry-level and experienced cybersecurity positions (figure 1). Reskilling programs, use of performance-based training, industry credential training, and the use of apprenticeship programs are the primary mitigation approaches to upskill existing workforces and address the workforce shortage. Training is also used to allow interested non-security professionals to move into security roles.5
- Global cybersecurity job vacancies grew by 350% from one million openings in 2013 to 3.5 million in 2021. Moreover, there were 3.5 million unfilled cybersecurity jobs in both 2022 and 2023. Of those positions, 750,000 were in the United States.6
The findings from global research indicate that an imminent threat is on the horizon, especially considering the rapid advancement of technologies such as generative artificial intelligence (AI). These technologies are vulnerable to exploitation by bad actors, making it crucial for cybersecurity professionals to be at the forefront of this battle.7
Recognizing individuals with transferable skills and talent and developing them into cyberprofessionals has been a go-to strategy for those building SMB security teams. Small enterprises have critical budget constraints around headcount, and promoting from within—from departments outside of cybersecurity—helps complete a team structure while offering promotion opportunities that would not be available otherwise.
To this end, a common thread in the research is the importance of cross-training. In its 2023 Official Cybersecurity Jobs Report, security enterprise Esentire reported that “A silver lining of mass redundancies (from the big layoffs in the technology sector) is a talent pool of recently unemployed workers with desired, transferable skills that would make them exceptional in cybersecurity roles.” Organizations can harness these skills, ensuring a smooth transition for these workers into cybersecurity positions by offering training and development programs. Similarly, non-security IT teams must shoulder some of the security burden and receive training in modern threat awareness, including phishing, social engineering, business email compromise (BEC), and financial fraud. These employees must also know how to protect and defend apps, data, devices, infrastructure, and people.
To achieve these aims and bolster the workforce, it would behoove enterprises to consult the NICE Framework from the US National Institute of Standards and Technology (NIST). The framework can empower enterprises to identify and implement targeted training programs, mentorship opportunities, and industry partnerships. It is a resource that can effectively transform an underutilized segment of the workforce into skilled professionals in both traditional IT and cybersecurity roles.8
The NICE Approach
The road to a secure enterprise is not paved with unskilled labor. Globally, employers in public and private sectors face the challenge of sufficiently staffing talented, skilled security and cybersecurity professionals to manage the risk exposure unique to each organization. It has become evident that cybersecurity professionals require a diverse skill set beyond simply security expertise to effectively navigate the complex cyberlandscape. One accessible approach for both SMBs and larger organizations is leveraging NIST’s NICE Framework.
In 2020, NIST released Special Publication (SP) 800-181 Rev. 1, Workforce Framework for Cybersecurity (NICE Framework).9 According to NIST, the framework “provides a set of building blocks for describing the Tasks, Knowledge, and Skills (TKS) that are needed to perform cybersecurity work by individuals or teams. Through these building blocks, the NICE Framework enables organizations to develop their cybersecurity workforces, and helps learners explore cybersecurity work and engage in learning activities to develop their capabilities.”10
The road to a secure enterprise is not paved with unskilled labor. Operationally, this free toolset can be used in myriad ways, including one championed by the US National Initiative for Cybersecurity Careers and Studies (NICCS), a division of the US Cybersecurity and Infrastructure Security Agency.11 There are several ways the NICE Framework can be used to help close the security skills gap for the workforce and mature an organization’s security program:
- Identify role gaps in the current security program. The US federal government partnered with the private sector to develop a comprehensive set of roles with corresponding knowledge and skill areas to fit any government or private sector role. By reviewing the roles for relevance and eliminating those that are not required (e.g., the Multi-Disciplined Language Analysis role may not be relevant to an enterprise in the food services industry), the remaining roles can contribute to a security program’s development and maturity. The predefined skill and knowledge areas are consistent with contemporary cyber and conventional security challenges.
- Write job descriptions using the role’s TKS lists. Due to the comprehensive nature of the TKS lists, they can be selectively utilized to craft a job description tailored to the specific role required. For example, there are just short of 90 knowledge areas for a security analyst, covering cryptography to supply chain to privacy laws. A job description can be created using the tasks, knowledge, and skills most relevant to the enterprise and the needs of the security program.
- Identify gaps in an external candidate’s knowledge, skills, and abilities as a data point in the hiring process. The TKS lists can be used to pre-screen a candidate’s CV and identify weaknesses. The objective of this step should not be to screen out candidates, but rather to determine whether there is enough knowledge and skills to transfer.
- Identify gaps in an internal candidate’s knowledge, skills, and abilities and create an individual development plan for the candidate. This might be the most crucial of the use cases in favor of the NICE Framework. If implemented as part of an internal repeatable process with relevant and regular milestone updates, the framework becomes a gap analysis and career-building tool, outlining possible career pathways into and within security.
NICCS offers an online toolset to help organizations map out the four components of the NICE framework:12
- Work Role Categories—Seven high-level groupings of common cybersecurity functions
- Work Roles—52 work groupings (designated by responsible or accountable)
- TKS Statements—More than 2,000 descriptions that describe the work to be done (the Task), what is required to perform that work (the Knowledge), and the Skill typically needed to perform the work area
- Competency Areas—11 clusters of related Knowledge and Skill statements that correlate with one’s capability to perform tasks in a particular domain
Work Roles and Role Categories
The NICE Framework lists 53 Work Roles across the seven Work Role Categories, with each role comprising 2,281 Tasks, Knowledge descriptions, and Skills. This is an almost exhaustive list, meaning that the framework implementer may not need to create additional work roles or TKSs.13
Competency Areas
The NICE Framework defines Competency Areas as “a cluster of related Knowledge and Skill statements that correlates with one’s capability to perform Tasks in a particular domain. Competency Areas can help learners discover areas of interest, inform career planning and development, identify gaps for knowledge and skills development, and provide a means of assessing or demonstrating a learner’s capabilities in the domain.”14
One value that Competencies offer is in the grouping of TKSs that cross Work Role Category boundaries. As an example, the Cyber Resilience Competency includes the skill of architecture, which is found in the work roles Cybersecurity Architecture (Design and Development) and Vulnerability Analysis (Protection and Defense.) This presents an opportunity to craft a job description by interrogating the TKSs across all Work Role Categories for a target Competency. Such a method could also be used to help identify transferable skills if it has proven difficult to locate a suitable candidate.
Competency Areas can also prove useful in career planning. For instance, a staff member may have their sights set on working in supply chain security; the TKSs offered in the Competency could lead them down the educational path to meet their goal.
Using the Framework
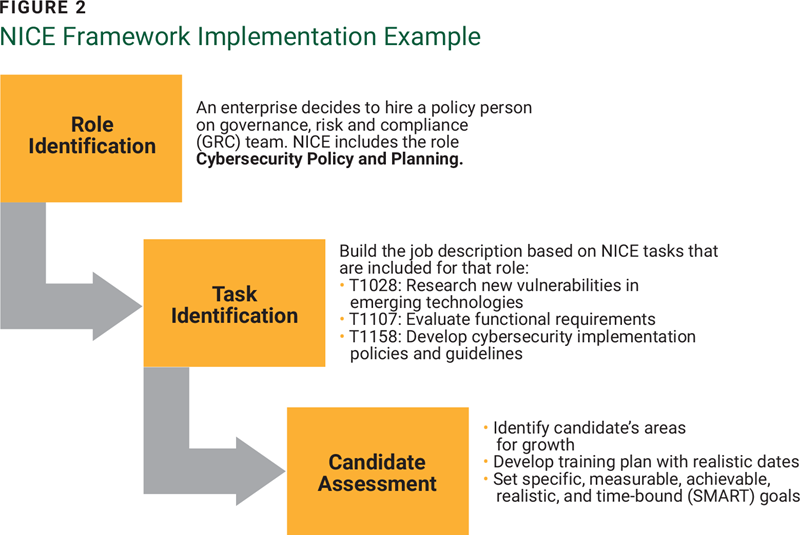
Many education and training providers focused on cybersecurity for higher education, K-12, and industry certification and training spaces use the NICE Framework.15 Because the framework is highly flexible and customizable, it can be deployed at an enterprise using several high-level steps. Some initial steps include:
- Role identification to identify the roles relevant to the security program. There are many predefined roles in the framework, reducing the need to create roles from scratch.
- Task identification to create an inventory of enterprise-specific tasks associated with the roles, knowledge areas applicable to the roles, and the skills needed to be successful. The NICE Framework already provides these for existing roles. However, organizations looking for more nuance can utilize custom TKSs tailored to their enterprise needs. These customized TKSs can encompass skills such as handling data subject access requests, understanding the specific consent management platform in use, and managing requests effectively.
- Candidate assessment by creating a system to identify a candidate’s strengths and weaknesses based on the TKS lists.
The human resources (HR) department, if applicable, is an important stakeholder in the use of this tool, not only for their subject matter expertise but also their access to the recruiting process and often the employee training program. As developing skills and knowledge areas will necessarily impact an employee, the HR expert will be a valuable guide through the internal processes, including legal and contractual considerations around governing law and, where applicable, potential union impacts.
Standardization
Originally, the NICE Framework’s greatest benefit was in the standardization of roles for the US government. The logic was that if the Department of Interior had an opening for a security analyst, someone from the Department of Energy could be hired without subjecting the candidate to unnecessary questions about knowledge, skills, and abilities. This also speeds up recruitment time, leaving roles open for less time. Onboarding was shortened too, since the general Knowledge, Skills, and Abilities (KSAs), which evolved into TKSs, were the same.
NICE: An International Framework
Over the years, the NICE mission and structure have evolved to address the needs of both the public and private sectors, including international enterprises and governments. The strategic plan16 for NICE includes the expansion of international outreach to promote the framework and the documentation of approaches being used outside of the United States. It coordinates internationally in several ways:17
- NICE engages with Five Eyes (FVEY) member countries in support of national cybersecurity workforce efforts.
- NICE is a member of the International Coalition of Cybersecurity Workforce Frameworks, whose goal is to drive consistency and coherent measures for domestic cybersecurity workforces.
- NICE also works with the US Department of State, USAID, and other organizations to engage with nations on cybersecurity workforce efforts.
While NICE serves as a comprehensive resource, it is important to note that other frameworks exist that may be better suited to a given organization. The European Cybersecurity Skills Framework (ESCF)18 and the US Department of Defense Cyber Workforce Framework19 may also be considered when selecting a framework approach.
Conclusion
Meeting the challenge of hiring qualified candidates to complete the buildout of a security program, or to keep one operational, requires a novel approach to the hiring process. In a buyer’s market, where demand for workers outpaces supply, obtaining resources may be more expensive and difficult. Building talent from nonstandard sources, such as internal help desks, application support, and project managers, through knowledge development with skills training is needed.
Hiring from within is an effective hiring strategy that improves organizational culture. The NICE Workforce Framework for Cybersecurity is an invaluable tool for implementing improved strategy and culture, ultimately bridging the cybersecurity skills gap.
Endnotes
1 Stephenson, G.; “The Employment Market Outlook for 2025: A Focus on Corporate America and Global Hiring Trends,” Gateway Recruiting, 9 January 2025,
2 Lightcast, The Lightcast Quarterly Cybersecurity Talent Report, 2024
3 ISACA®, “ISACA Live | Ask a Cybersecurity Recruiter,” 16 October 2024
4 Meineke, M.; “The Cybersecurity Industry Has an Urgent Talent Shortage. Here’s How to Plug the Gap,” World Economic Forum, 28 April 2024
5 ISACA©, State of Cybersecurity 2024, 1 October 2024
6 Farber, M.; “Cybersecurity Jobs Report: 3.5 Million Unfilled Positions in 2025,” The Associated Press, 14 April 2023
7 Hutchinson, R.; “” Forbes, 31 July 2024
8 Farber; “Cybersecurity Jobs Report”
9 National Institute of Standards and Technology, SP 800-181 Rev. 1, Workforce Framework for Cybersecurity (NICE Framework), USA, November 2020
10 National Institute of Standards and Technology, SP 800-181
11 National Initiative for Cybersecurity Careers and Studies, Workforce Framework for Cybersecurity (NICE Framework), USA, June 2024
12 National Initiative for Cybersecurity Careers and Studies, Workforce Framework for Cybersecurity
13 National Institute of Standards and Technology, SP 800-181
14 National Institute of Standards and Technology, Nice Framework Competency Areas: Introduction and Proposed List, USA, 21 June 2023
15 National Institute of Standards and Technology, “NICE Framework Resource Center” USA
16 National Institute of Standards and Technology, Strategic Plan (2021-2025), USA, 23 June 2023
17 National Institute for Standards and Technology, “International Cybersecurity Workforce Framework Resources,” USA, 2024
18 European Union Agency for Cybersecurity, European Cybersecurity Skills Framework (ECSF)-User Manual, European Union, 19 September 2022
19 Chief Information Officer, U.S. Department of Defense, “The DoD Cyber Workforce Framework,” USA
JAMES BAIRD, CISM, CRISC, CISSP
Is a visionary public speaker and author who specializes in security program turnarounds and greenfield program builds. Baird has 29 years of experience in technology across retail, fintech, telecommunications, and hospitality organizations. He has spent 15 years in global transformative chief information security officer (CISO)/chief security officer (CSO) roles in small, medium, and large US domestic and multinational enterprises.