It may seem that the game of chess has little to do with cybersecurity governance, risk, compliance, and strategy, but there is an interesting connection. The opening moves in the game of chess can be used to map controls specified in ISACA’s COBIT® framework1 to the ISO/IEC 27001:2022 standard2 outcomes. Of the many opening moves available in the game of chess, the Queen’s Gambit3 may prove most useful in drawing this analogy.
Generally, the role of information security is well understood within organizations. For example, if an organization’s board of directors (BoD) wants to go public, organizations must consider how the change in priorities would impact the information security management system (ISMS). However, strategic governance requires more than ticking boxes to achieve compliance. Its purpose is to ensure that an organization is properly managed and focused on long-term goals for creating stakeholder value. It is clear that COBIT and ISO/IEC 27001:2022 have left the IT silo and now provide invaluable guidance in the enterprise strategy arena.
A successful cybersecurity strategy depends on achieving goals in three key areas:
- Awareness—Employees must be aware of security standards and frameworks in practice and have a deep understanding of security measures, that is, educate the people and they will fix the process.
- Belief—Enterprise leadership must authentically believe in and advocate for the framework/standard and enforce the adoption of its controls.
- Culture—A culture of cybersecurity-compliant values must be embedded in the organization—technical skills alone will not create value for stakeholders. A security-and compliance-driven culture can be fostered through the adoption of cybersecurity awareness training as an onboarding practice. Additionally, a team must be established to integrate the ISMS with ISO/IEC 27001:2022 and COBIT and incorporate the changes in business operations.
Alignment with organizational values is vital for enhancing innovation and creativity, boosting performance, increasing productivity, and contributing to personal and professional growth. This also creates a dynamic culture of learning, improvement, and active engagement with all stakeholders, team members, and employees, with the ultimate goal of enhancing security and increasing value.
The changes and realignment from ISO/IEC 27001:2013 to ISO/IEC 27001:20224 have made ISO/IEC 27001:2022 and COBIT useful as strategic tools, particularly for organizations that need to strengthen their governance and streamline enterprise operations. The opening chess move, the Queen’s Gambit, is a strategy that balances risk and reward and helps enterprises adopt governance strategies that encourage operational excellence. As an analogy, it shows how an organization that needs to have control over its technology environment can implement a governance framework to create checks and balances based on the policies and standards that determine enterprise procedures and guidelines. Much like the Queen’s Gambit in a game of chess, governance in an enterprise requires a substantial sacrifice to gain an advantage over the inherent risk associated with IT.
The Queen’s Gambit
The Queen’s Gambit is probably the most popular gambit in chess, and although most gambits are said to be unsound against perfect play, the Queen’s Gambit is often considered the exception. Its aim is to strengthen the player’s defenses and provide an attack advantage.5
As shown in figure 1, White appears to temporarily sacrifice a C-pawn to gain control of the center of the board. The Queen’s Gambit works as follows:
- d4 d5—White’s pawn on d4 and Black’s pawn on d5 establishes a fight for the center.
- c4 c6—White offers the c4 pawn triggering the Queen’s Gambit. The intention is to lure Black’s d5 pawn away from the center. But Black moves a pawn to c6 instead, denying the gambit.
- Kn f3—White moves the knight to f3, indirectly supporting control of the center.
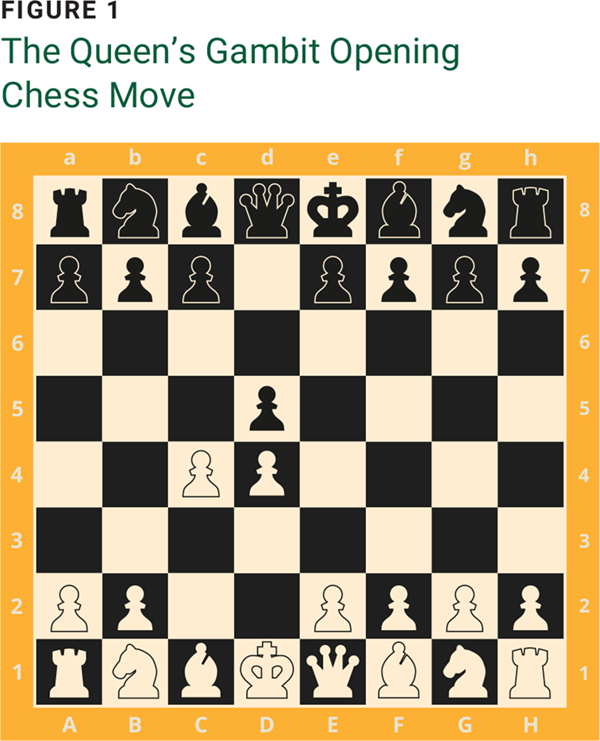
If Black were to accept the Queen’s Gambit, taking White’s pawn on c4, it would temporarily give Black an extra pawn—but it would give White an advantage in controlling the center. The Queen’s Gambit entails a degree of work and sacrifice to gain an advantage over inherent risk. The same is true when it comes to developing an enterprise strategy associated with the use of IT and related technologies. The aim of the gambit is to strengthen White’s defenses. Similarly, an enterprise aims to defend against cyberattacks.
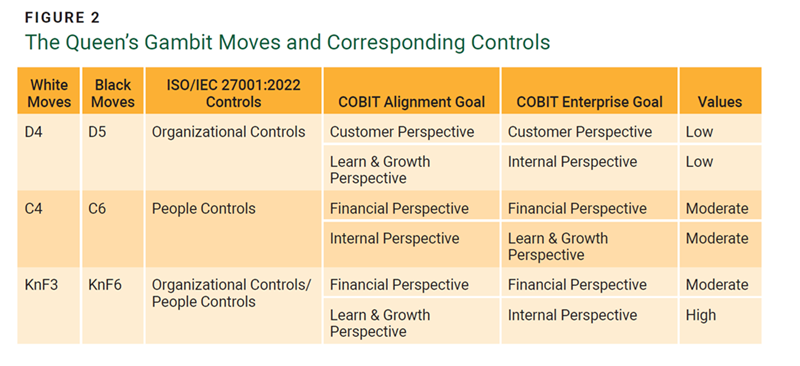
The Queen’s Gambit moves are explained with reference to ISO 27001:2022 controls, COBIT Alignment Goals (AGs), and COBIT Enterprise Goals (EGs) in figure 2.
There are several factors to consider when viewing ISO/IEC 27001:2022 and COBIT through the lens of the Queen’s Gambit:
- The need to integrate IT governance with overall enterprise strategy through COBIT and ISO/IEC control objective links as they relate to the opening chess move, the Queen’s Gambit, and measure control performance
- The need for knowledge innovation and effective deployment, governance, and management of enterprise IT through enterprise governance of IT (EGIT)
- The need to position the organization to strengthen internal operations through principled governance that will prepare it for adoption of any technology
- The need to ensure that digital transformation processes are not disrupted due to cyberattacks or threats to intellectual property
- The need to provide visible assurance to stakeholders throughout strategic management consultations and decision making (this visibility can be observed in the Queen’s Gambit)
- The need to develop key performance indicators (KPIs) that can be applied to individual employees or organizational units for appraisals and functional assignments
Rather than asking what enterprise IT can deliver, organizations should be asking how they can use enterprise IT to their benefit. The focus should be on the organizational value of enterprise IT, enterprise IT cost optimization practices, investment prioritization, IT project finance and sourcing options for resources, project benefit realization, and innovation accounting. These concepts can be better understood by mapping COBIT to ISO/IEC 27001:2022.
The Governance and Management Objectives in COBIT
COBIT provides a comprehensive framework that helps enterprises achieve their goals and deliver value through effective governance and management of enterprise IT. The governance and management objectives in COBIT are grouped into five domains. These domains are expressed through verbs that convey the key purpose and areas of activity of their objectives (e.g., Governance objectives are grouped in the Evaluate, Direct, and Monitor [EDM] domain).6 In this domain, the governing body evaluates strategic options, directs senior management in terms of the chosen strategic options, and monitors the strength of the three essential components: awareness, belief, and culture.
Management objectives are grouped into four domains:7
- Align, Plan, and Organize (APO) addresses the overall organization, strategy, and supporting activities for enterprise IT.
- Build, Acquire, and Implement (BAI) addresses the definition, acquisition, and implementation of IT solutions and their integration into enterprise processes.
- Deliver, Service, and Support (DSS) addresses the operational delivery and support of IT services, including security.
- Monitor, Evaluate, and Assess (MEA) addresses performance monitoring and conformance of IT with internal performance targets, internal control objectives, and external requirements.
With COBIT, ISACA delved into the enterprise strategic governance area of any enterprise IT or technology organization. The ISO/IEC followed suit, making their standard clearer for enterprise governance.8
Updates to the ISO/IEC 27001 Framework
In October 2022, ISO published an updated version of ISO/IEC 27001.9 ISO/IEC 27001:2022 includes the same number of clauses as ISO/IEC 27001:2013, but their contents have changed slightly. The changes help align ISO/IEC 27001 with four other ISO management standards:
- Organizational controls (Org C) – 37 controls 10
- People controls (Peo C) – 8 controls11
- Physical controls (Phy C) – 14 controls12
- Technological controls (Tec C) – 34 controls13
Figure 3 shows the score values of mapping the realigned and reorganized ISO/IEC 27001:2022 controls to COBIT. This mapping can be used to develop a balanced scorecard (BSC).
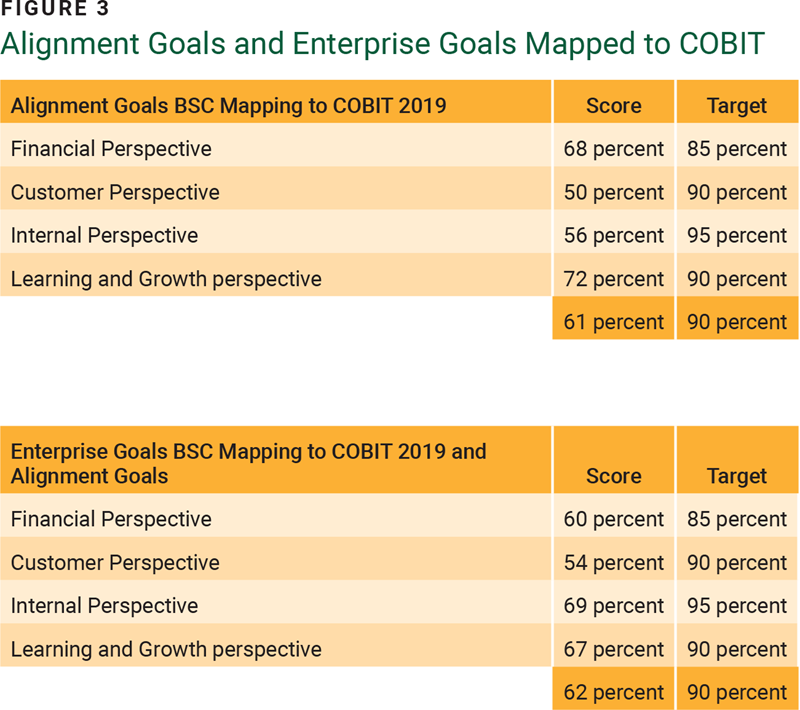
The BSC of COBIT AGs shows low values, but the scores are increased with the value inputs from the ISO/IEC 27001:2022 people control structures.
Further exercises with input values from ISO/IEC 27001:2022 controls can be compared to a chess game opening with the Queen’s Gambit to strengthen the strategic understanding of mapping ISO/IEC 27001:2022 to COBIT for enterprise governance strategy. With the values in organizational controls and people controls, the alignment and reorganization of ISO/IEC 27001:2022 with COBIT becomes more evident and important in addressing enterprise governance strategies, as the first two and the last core domains in COBIT (figure 4) are reflective of these new approaches with input values in ISO/IEC 27001:2022.
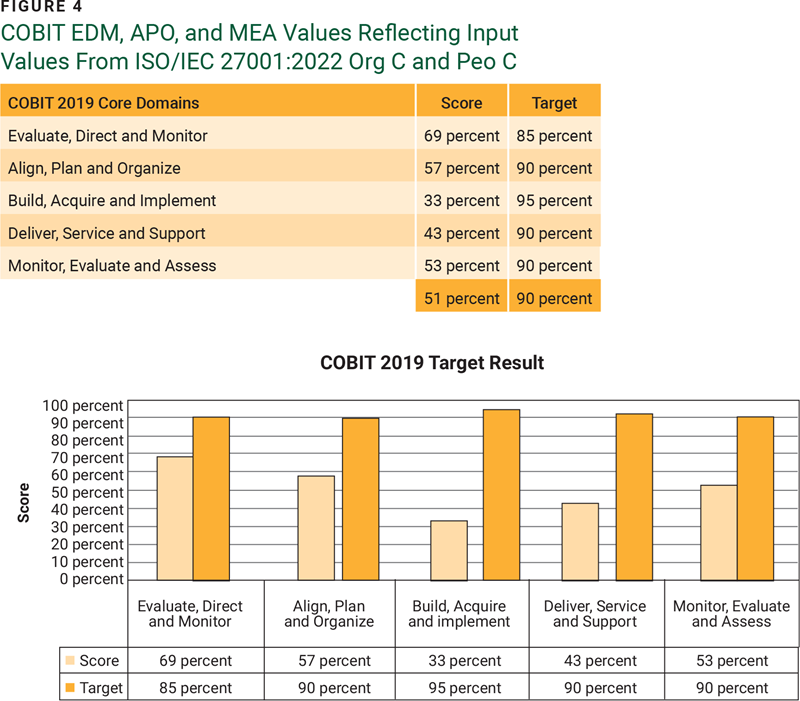
Organizations can determine their goals and address challenges based on the COBIT core domain results from the value inputs from ISO/IEC 27001:2022.
Being compliant is far from being secure. Progress should be measured against potential, not past, performance. Therefore, compliance offers an organization a means to understand the depth of its issues and pain. Essential procedures are required to establish a cybersecurity program. Mapping these control points to COBIT can be used to develop a BSC system for cybersecurity strategic alignment to the organization.
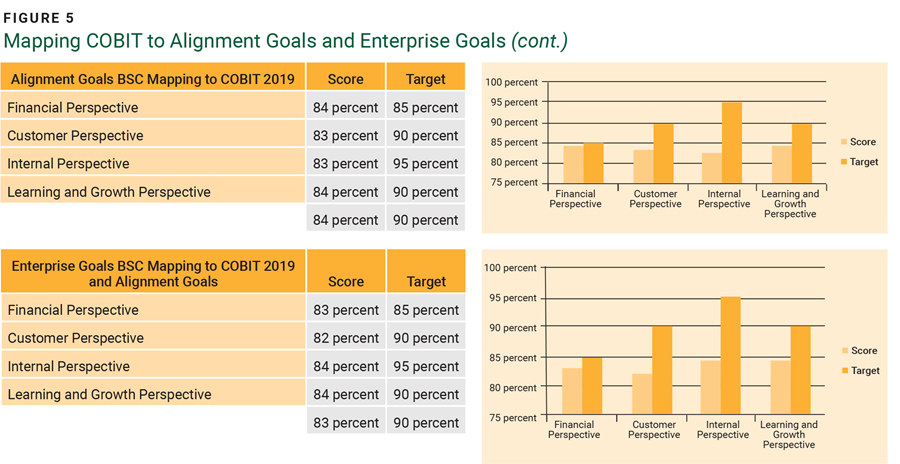
The result and summary of the BSC with respect to the AG and EG numerical values of COBIT are displayed in figure 5.
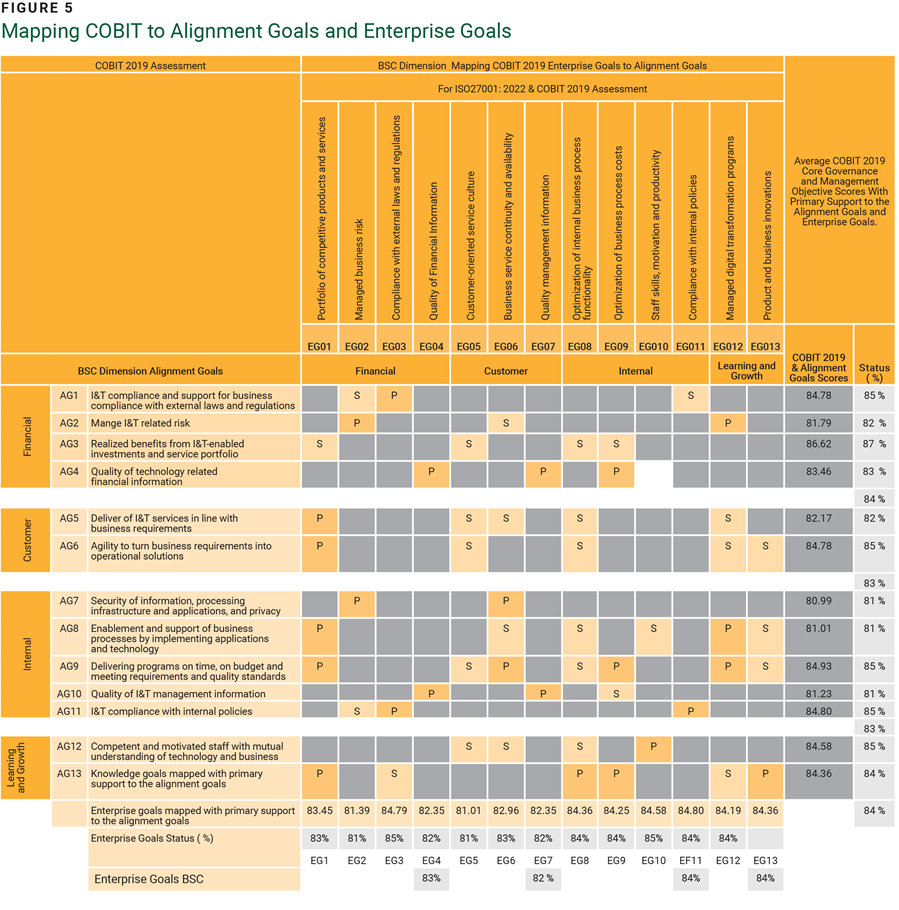
Consider the relationships of some common strategic governance goals:
- AG09—Delivering programs on time, on budget and meeting requirements and quality standards and EG06—Business service continuity and availability address, enhance, and support business continuity management as a primary function or have a primary relationship with each other in EGIT.
- AG09 and EG09—Optimization of business process costs is another key relationship and should be a primary function in program management of EGIT. This relationship should be changed from secondary to primary.
The updates or changes are highlighted in yellow (depicted as P and S) in figure 5. This type of strategic focus should be the driving force in this exercise, as the game of chess encourages the player to think ahead about their opponent’s moves.
Using COBIT to Address Digital Disruption and Privacy Concerns
The COBIT framework helps organizations understand their technological needs and provides guidelines on how to fulfill those needs. Organizations that build strong defenses against threats and ensure that digital transformation processes are not disrupted due to cyberattacks will position themselves as leaders in technological innovation.
Strategic technology trends have significant disruptive potential and set the stage for innovative digital disruptions over the next five years. The tumultuous COVID-19 pandemic highlighted the criticality of digital transformation. No longer an option, it has become an organizational imperative integral to competitiveness and relevance in a dynamic market.
In cybersecurity, navigating conflicts and negotiations requires a foundation of facts and an understanding of the systems, risk, and technical implications involved. By wielding knowledge as a guiding force, practitioners can navigate conflicts adeptly and foster collaborative resolutions that benefit all parties involved.
Driving digital transformation in an enterprise is a difficult process without an EGIT culture. With this understanding from the BSC perspective and a focus on the primary supporting values, practitioners can determine where their enterprise and their industry face a significant risk of disruption to revenue or customer experience. At the core of this transformation are the customer desires, expectations, and experiences that should guide an enterprise’s digital strategy. The power of technology can be utilized to personalize these experiences, ensuring that each interaction is tailored to customer preferences.
Integral to this journey are collaboration and innovation. A collective effort is needed to ideate, create, and deploy solutions that resonate with evolving customer needs, thereby creating value. An innovative mindset should be the compass when navigating the digital landscape. In essence, digital transformation is the embodiment of perpetual agility that enables readiness to adapt to ever-changing customer demands. Digitally agile enterprises transcend the legacy boundaries of technological knowledge, skills, and ideas. “Disruption requires creating a new basis (in a competition), usually parallel to any existing paradigm.”14
Conclusion
COBIT, particularly in its EDM domain, has addressed the shortcomings of poor organizational governance and made the framework easier to adapt and adopt as an umbrella framework for EGIT. COBIT helps identify strategic opportunities, build relationships with executive sponsors, and manage people, data, and technology. The vision and strategy driver scores are achieved from the mapping exercise of ISO 27001:2022 to COBIT.15
The results from mapping COBIT Governance and Management Objectives to Alignment Goals and then to Enterprise Goals show an enriching perspective of the EGIT and strategy from the COBIT framework. The framework and the exercise help in strategic learning, which consists of gathering feedback, testing the hypotheses on which a strategy is based, and making necessary adjustments.
The BSC perspectives help the organization educate staff, communicate strategy, and measure outcomes through improvements in financials and responses or growth of customers. The assessment results can be drilled down to the input values with a backward review of the mapping values used in determining the root cause of having low values from a set of mapped data in ISO/IEC 27001:2022 control objectives and questions. This will form a basis for developing an action plan as needed by the enterprise.
The importance of measuring performance and strategically integrating IT governance with overall governance through control objective linkages between the two frameworks can be seen in the Queen’s Gambit chess game opening, as it shows the need to strengthen enterprise cybersecurity processes and technology by means of careful planning, risk taking, and sometimes sacrifice. Incorporating COBIT in a strategic plan to achieve an objective and carefully weighing tactical options to implement the strategy (as in the Queen’s Gambit) is paramount to enterprise security and success.
Endnotes
1 ISACA®, COBIT®; 2019 Framework: Introduction and Methodology, USA, 2019
2 International Organization for Standardization (ISO), ISO/IEC 27001:2022 Information security, cybersecurity and privacy protection —Information security management systems—Requirements, Edition 3, 2022
3 The Chess Website, “Queens Gambit”
4 Anoruo, C.; “Employing COBIT 2019 for Enterprise Governance Strategy,” ISACA, 28 October 2019
5 The Chess Website, “Queens Gambit”
6 ISACA, COBIT 2019 Framework
7 ISACA, COBIT 2019 Framework
8 Anoruo; “Employing COBIT 2019”
9 ISO/IEC, ISO/IEC 27001:2022
10 ISO/IEC, ISO/IEC 27001:2022
11 ISO/IEC, ISO/IEC 27001:2022
12 ISO/IEC, ISO/IEC 27001:2022
13 ISO/IEC, ISO/IEC 27001:2022
14 Ekekwe, N.; “#AimHigher – Move Upstream,” Tekedia, 7 October 2019
15 Anoruo; “Employing COBIT 2019
CHRISTOPHER C. ANORUO, CISM, CGEIT, CRISC
Is the chief executive officer (CEO) of TRAFTEC Ltd., a cybersecurity company he cofounded. Previously, he was the executive director of technology and operations at KATEC Consulting Ltd. He has also worked in various positions in the telecommunication and banking industries in West Africa. He was the pioneer enterprise cybersecurity manager at Econet Wireless Nigeria, Vmobile Nigeria, and Airtel Nigeria; he led the West African security, asset, and risk management (SARM) program at IBM; and he served as an information security consultant with IBM Global Business Services. Anoruo has contributed to the ISACA® Certified Information Security Manager®; (CISM®), Certified in the Governance of Enterprise IT®) (CGEIT®), and Certified in Risk and Information Systems Control™ (CRISC™) exams. He has also participated in ISACA certification projects and has been part of the ISACA Test Enhancement Committee since 2005, helping create exam questions and review exam manuals.