The introduction of the Internet of Things (IoT) in the healthcare industry has transformed the delivery of healthcare. The integration of IoT facilitates the efficient delivery of patient care through wearable devices, smart medical devices, telemedicine, and remote patient monitoring. However, these devices are also susceptible to cyberattacks. Healthcare involves various critical types of personal information, including the age and physical condition of the patient. If there is a breach, healthcare infrastructure and patient safety can be negatively impacted.1
The term zero trust (ZT) was coined in 2010 by John Kindervag to address security in IT environments and workplaces. The US National Institute of Standards and Technology (NIST) defines zero trust as follows: “Zero Trust (ZT) provides a collection of concepts and ideas designed to minimize uncertainty in enforcing accurate, least privilege per-request access decisions in information systems and services in the face of a network viewed as compromised.”2
The importance of implementing ZT in the healthcare industry is clear, given the current security concerns related to the IoT healthcare infrastructure, the benefits of implementing a ZT framework, and the regulatory and compliance aspects of healthcare, such as the US Health Insurance Portability and Accountability Act (HIPAA). With ZT, no device, user, workload, or system is trusted by default, notwithstanding the location from which it is operating, whether inside or outside the security perimeter. This model can be deployed to meet the healthcare industry’s current security challenges by enforcing the default deny measure based on the ZT concept.
Security Challenges in IoT-Enabled Healthcare
The IoT has transformed healthcare delivery, patient monitoring, and telemedicine. However, this innovation has introduced security challenges that can be life-threatening for patients and can lead to privacy concerns when healthcare data is exposed to cyberattack.3
Research has identified three critical security challenges in the IoT-enabled healthcare infrastructure that are likely to impact the security of patients' data and the reputation of the healthcare facility:
- Privacy risk—IoT devices used in healthcare are interconnected and contain patients' highly sensitive data, making patient privacy and the security of such data a priority. According to the European Union’s General Data Protection Regulation (GDPR),4 it is vital to develop and apply technical mechanisms that ensure the protection of individuals’ data when it is being processed. The GDPR is enforced across all EU member states, with the purpose of ensuring the uniform protection and privacy of healthcare data and connected IoT devices.5For instance, failure to implement end-to-end encryption in the collection, transmission, and storage of patient data can lead to the loss of confidential patient information, as occurred in the 2024 cyberattack on the UK’s National Health Service provider Synnovis.6
- Device security and interoperability—Many IoT devices used in healthcare have weak security protocols, largely because of manufacturers’ unwillingness to adopt best practice security standards. This may be attributed to the lack of accepted global standards for IoT manufacturers in the healthcare space. The need for these devices to integrate seamlessly and communicate with one another can create security gaps leading to vulnerability.7
- Regulatory concerns—Regulations are not a tick-the-box routine; they can be deployed to minimize the impact of a cyberattack. Regulations such as HIPAA and GDPR can help secure data in the healthcare space, reducing security concerns, minimizing variations in the safety of different devices and systems, and improving patient safety and outcomes. For instance, unpatched vulnerabilities in connected medical devices, manufacturers’ default passwords, and devices with inadequate security parameters can be exploited by attackers when manufacturers fail to adhere to regulatory standards.
Understanding Zero Trust
The ZT concept has proved to be reliably secure across all global IT infrastructure and is arguably one of the best ways to protect personally identifiable information (PII).8 According to NIST, ZT architecture is not a single deployment plan; it should include devices, infrastructure components, applications, and virtual and cloud components.9
Because ZT assumes that attackers are within the infrastructure and that assets and components of the infrastructure should not be treated differently, ZT can minimize the attack surface of the IoT healthcare infrastructure. ZT encompasses the identification of person and nonperson entities, credentials, access management, operations, end points, hosting environments, and the interconnecting infrastructure.
The emphasis is on verifying identity, permitting access only where necessary, and minimizing areas where trust is assumed. This is done while ensuring that services are accessible and authentication processes are quick. Access rules are detailed, and specific permissions are required for a given task. In the model illustrated in figure 1, a user requires access to a healthcare IoT resource. Permission is granted through a policy decision point (PDP) and the related policy enforcement point (PEP).
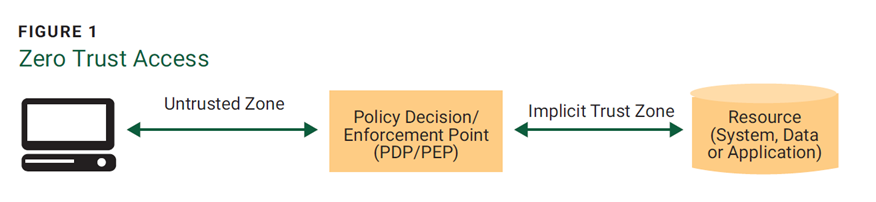
Source: National Institute of Standards and Technology (NIST), NIST Special Publication (SP) 800-207, “Zero Trust Architecture,” 2020, Reprinted courtesy of the National Institute of Standards and Technology, U.S. Department of Commerce.
This ZT principle aims to implement security controls that are closely interconnected, removing wide-area perimeter controls. This makes ZT the ideal approach for IoT-enabled healthcare.
Zero Trust Maturity Model
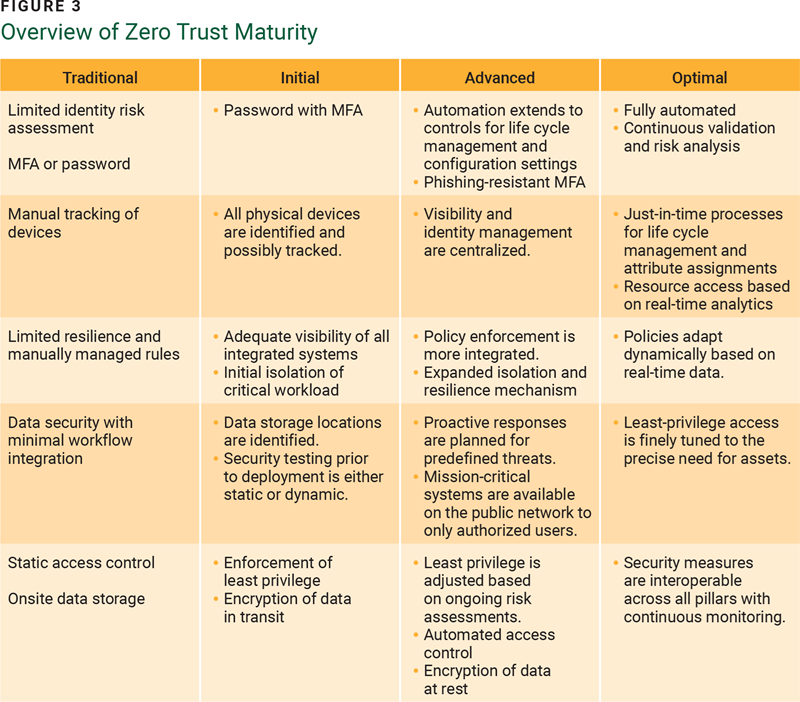
The ZT maturity model recommended by the US Cybersecurity and Infrastructure Security Agency includes a number of critical components: identity, devices, networks, applications and workloads, and data.10 Starting from a traditional baseline, maturity can be achieved in three stages: initial, advanced, and optimal (figure 2).
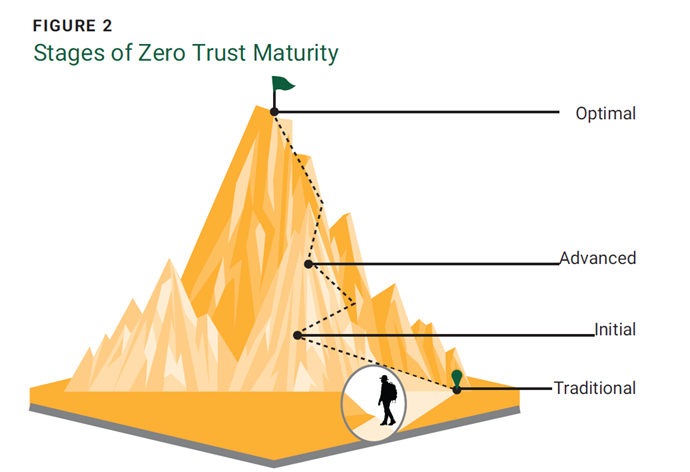
Source: Cybersecurity and Infrastructure Security Agency, “Zero Trust Maturity Model,” USA, 2023
Each subsequent stage demands increasingly higher levels of protection, detail, and complexity (figure 3).
A Systematic Approach to Implementing Zero Trust in IoT-Enabled Healthcare Systems
ZT has the ability to remediate cyberbreaches that are likely to impact the confidentiality, integrity, and availability of PII in the IoT healthcare infrastructure.
NIST recommends that enterprises gradually adopt ZT principles, enact procedural changes, and integrate technological solutions that safeguard their data assets and business operations based on specific use cases.11
Using the ZT framework and a physiotherapy device as an example, the security parameters and other components of a healthcare infrastructure can be analyzed. The software component of the device routes communication traffic to the relevant PEP to access the requested system through the policy administrator. The gateway of the physiotherapy device communicates with the policy administrator through the policy engine and permits only those communication paths the policy administrator has authorized (figure 4).
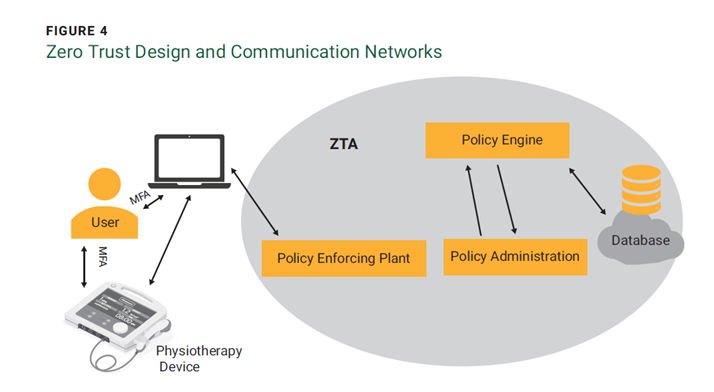
Critical data accessed from outside the ZT infrastructure requires permission within ZT parameters. The PEP is split in two when there is communication between both system and proxy. Every physiotherapy device issued by the enterprise is equipped with a device agent that manages connections, and each resource is accompanied by a component positioned directly in front of the gateway to extract data for use. Implementing ZT yields several significant benefits that can strengthen security defenses, protect patient data, ensure regulatory compliance, and enhance the overall reliability and trustworthiness of healthcare systems, leading to improved patient care and outcomes. To realize the benefits of ZT, the following steps are required:
- Microsegmentation of the network infrastructure—The basis of ZT infrastructure is the microsegmentation of individual hosts within the network to provide adequate security between firewall boundaries. However, this can be complex in an IoT healthcare infrastructure.12 It may be impossible to enforce policy in legacy applications; for newer systems, a more clustered model can be deployed by placing a set of routers or a next-generation firewall in front of a set of hosts to filter their traffic.13 However, it may also be possible to implement workaround policies in legacy systems as well as new applications.14 A mix of microsegmentation techniques can minimize the attack surface when there is adequate management of the application interfaces.
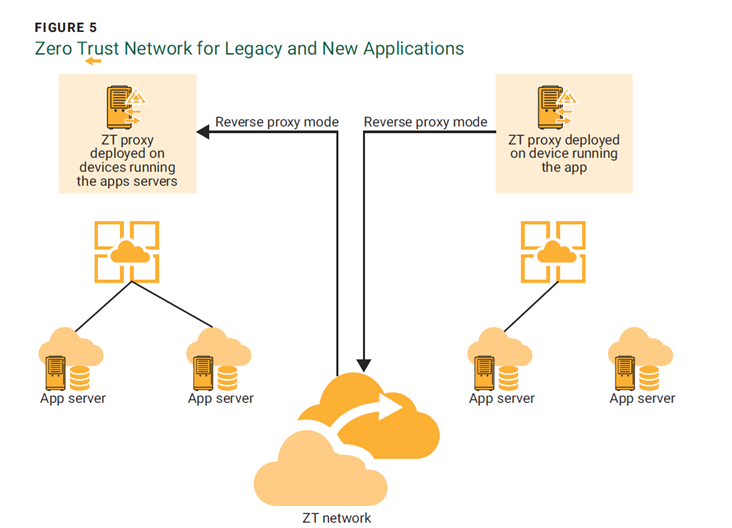
- Integration of new and legacy IoT devices—There has been debate about the interoperability of the ZT concept in legacy and new IoT devices in the healthcare setting. One proposal is to deploy a proxy server at the application interface to streamline the access parameters of the legacy and new devices (figure 5).15 This model can protect application security as well as support the legacy system to avoid the cost of procuring new IoT healthcare devices.
- Identity management—Identity management is critical, as the emphasis in ZT is to deny access to unajavascript:void(0);uthorized users. The ZT model based on identity proves effective within the resource portal model, as device identity and status serve as supplementary data to support access decisions.16 The server must be allowed to verify the user’s identity by creating a virtual private network (VPN) tunnel between the user and the resource or application being accessed.17
- Regulatory compliance—The United States Department of Health and Human Services and NIST recommend ZT as a way forward for healthcare enterprises, which means that the ZT concept complies with existing regulations. In the United States, HIPAA’s administrative, physical, and technical safeguards that cover data access, storage, handling, and management can be achieved with the implementation of ZT in IoT-enabled healthcare settings.
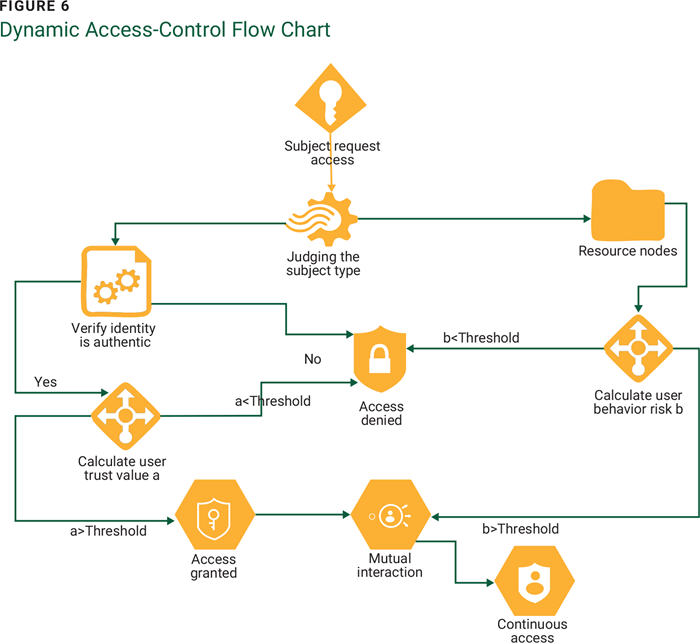
ZT relies on multifactor authentication (MFA). A dynamic access-control engine (figure 6) that manages and evaluates the access permissions of all subjects and enforces dynamic access in a ZT environment is a better alternative than the traditional static access-based permission.18 Humans are the weakest link, and network configurations do half the work when it comes to security and access enforcement.
Conclusion
The most prevalent type of cyberattack in the healthcare industry is ransomware.19 With billions of interconnected devices, the risk of exposing PII is growing. However, by embracing a ZT approach, the risk can be mitigated. In the IoT-enabled healthcare infrastructure, ZT opens the door to a new era of end-to-end protection. By adopting ZT, the industry takes a proactive step toward safeguarding patient data, preserving patient trust, and securing the future of healthcare.
The challenges related to legacy devices, interoperability, user experience, and regulatory compliance are arguably not substantial enough to discourage adoption of the ZT approach. Existing regulatory frameworks such as HIPAA have proved that regulations alone are insufficient to protect patients' privacy in the healthcare setting. The adoption of multiple security alternatives can be the solution to the incessant cyberattacks plaguing the healthcare industry.
Endnotes
1 Wang, Z.; Yu, X.; et al.; “Research on Medical Security System Based on Zero Trust,” Sensors, vol. 23, iss. 7, 2023, p. 3774
2 National Institute of Standards and Technology (NIST), NIST Special Publication (SP) 800-207 Zero Trust Architecture, USA, 2020
3 Gopalan, S.S.; Raza, A.; et al.; “IoT Security in Healthcare Using AI: A Survey,” 2020 International Conference on Communications, Signal Processing, and their Applications (ICCSPA), IEEE, 2021, p. 1–6
4 Regulation (EU) 2016/679 of the European Parliament and of the Council of 27 April 2016 on the protection of natural persons with regard to the processing of personal data and on the free movement of such data, and repealing Directive 95/46/EC (General Data Protection Regulation [or GDPR]) (OJ L 119, 4.5.2016, p. 1)
5 Chen, B.; Qiao, S.; et al.; "," IEEE Internet of Things Journal, vol. 8, iss. 13, 2020, p. 10248–10263
6 Casey, I.; “NHS Confirms Patient Data Stolen in Cyber Attack,” BBC, 24 June 2024
7 Gupta, A.; The IoT Hacker’s Handbook: A Practical Guide to Hacking the Internet of Things, Apress, USA, 2019
8 Edo, O.C.; Ang, D.; et al.; “A Zero-Trust Architecture for Health Information Systems,” Health and Technology, vol. 14, 2023, p. 189–199
9 NIST, SP 800-207
10 Cybersecurity and Infrastructure Security Agency, “Enhancing Infrastructure Security Through Zero Trust Architecture,” USA, 2022
11 NIST, SP 800-207
12 Tyler, D.; Viana, T.; "Trust No One? A Framework for Assisting Healthcare Organizations in Transitioning to a Zero-Trust Network Architecture," Applied Sciences, vol. 11, iss. 16, 2021, p. 7499
13 Uttecht, K.D.; “Zero Trust (ZT) Concepts for Federal Government Agencies,” 2020
14 Haber, M.J.; Privileged Attack Vectors, Apress, USA, 2020
15 Tyler; “Trust No One?”
16 NIST, SP 800-207
17 Uttecht, “Zero Trust Concepts”
18 Wang; “Research on Medical Security”
19 Edo; “A Zero-Trust Architecture”
SIXTUS DAUDU, CDPSE, ITIL FOUNDATION
Is a certification officer at Age Check Certification Scheme, where he assists in conducting audits in compliance with the UK Digital Identity and Attributes Trust Framework (DIATF). He is also a cybersecurity engineer at 4D Health Science, focused on developing and implementing information security strategies in preparation for the US Federal Risk and Authorization Management Program (FedRAMP). He has previous experience in the financial industry and is passionate about regulatory frameworks, identity management, and the roles they play in shaping the overall security of information systems.



