Risk culture refers to the system of beliefs, values, attitudes, and behaviors that characterize an enterprise and shape its approach to risk management and decision making.1 It is an asset that must be established, managed, and measured like any other internal process. Risk attitude,2 or the willingness to face or accept risk, is an intrinsic element of the enterprise. The practical application of methods for dealing with risk is the tangible expression of organizational culture, and its effect must be measured to compare different risk management capabilities. Risk attitude must be declared a priori by senior management and is the foundation for the establishment of a risk management system.3
How the system is implemented depends on the organizational culture. The effectiveness of the implementation is demonstrated by the risk profile,4 which is built by adopting an appropriate framework. In the case of cybersecurity risk, an excellent example of an applicable methodology is the US National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF) 2.0.5 Unlike the risk profile, risk culture is more difficult to define, leading to complexity when attempting to measure it directly. It is easier to apply an indirect approach that involves evaluating processes or measurable elements that characterize the culture. Effectiveness is a measurable element. For example, if those in the risk management system influence decision-making processes in a nonobjective way—that is, not based on evidence or facts—this could lead to ineffective risk prevention.
Risk culture can influence the decision-making process, and choices that are not based on the level of risk can generate vulnerabilities. By identifying these vulnerabilities and associating them with specific areas of risk culture, areas requiring improvement can be determined. To measure risk culture in the absence of any material, tangible, or concrete factors, qualitative evaluation methods must be adopted. The Capability Maturity Model (CMM) is the first choice for this purpose.6 The areas of risk culture that should be assessed are the business process governance activities that are most influenced by the subjective decision-making behaviors of senior management.
The Maturity Model in Risk Culture
The vulnerability assessment of an action is inversely related to the implementation maturity assessment of that action. While maturity represents the degree to which a goal is achieved, vulnerability is a complementary representation of what is missing from the goal. Whatever methodology is adopted, it cannot be limited to only labels that measure the level of maturity; it must have a numerical base large enough to represent cyclical evaluations over time to understand which areas need improvement. Numerical precision is not necessary because the indicators must be analyzed according to the trend of the phenomenon and not by their absolute value.
Risk culture can influence the decision-making process, and choices that are not based on the level of risk can generate vulnerabilities.When deciding which maturity levels to use, it is preferable to choose those that offer a sense of how behaviors evolve from complete disinterest in, to full awareness of, the benefits of following a certain action plan. The ability to behave in a progressively more risk-aware manner is what is assessed. Risk culture maturity levels can be classified as follows:7
- Vulnerable—Behavior that lacks attention to or trust in risk management issues; acceptance of incident risk instead of prevention; no planning
- Reactive—Little attention to prevention and research into the causes that lead to incidents; decisions made according to a minimum cost logic; search for the culprits rather than the causes; attention to performance
- Compliant—Attitude based on fear of consequences, with a formal and regulation-driven approach to risk; prevention driven by fear of harm; focus on compliance
- Proactive—Awareness of the importance of managing risk, with a holistic view of internal processes, by providing adequate prevention; prevention guided by risk awareness; risk-based planning
- Resilient—Experiencing risk with awareness of the consequences and the need for cooperation and integration between processes, transparency, and the sharing of results; proactivity and continuous improvement based on risk; decisions always based on risk
Each level is not assessed in a binary manner (i.e., “achieved” or “not achieved”) but rather through the degree of adequacy achieved according to an increasing progression of specific achievements toward full maturity. The degree of maturity is easily evaluated through a percentage scale ranging from a minimum to a target.
Risk Culture Assessment Matrix
The considerations for measuring enterprise risk culture are summarized in a matrix in figure 1. Risk management capabilities are placed in the rows of the matrix, while maturity levels are placed in the columns. Each cell contains descriptive text of the maturity objective represented by that cell. The evaluation proceeds progressively in rows, from one column to the next, with the maturity level increasing only when the cell target has been reached. This is not an absolute evaluation of the degree of maturity of the cell but the result of weighting the various phenomena observed for that area and level of maturity.
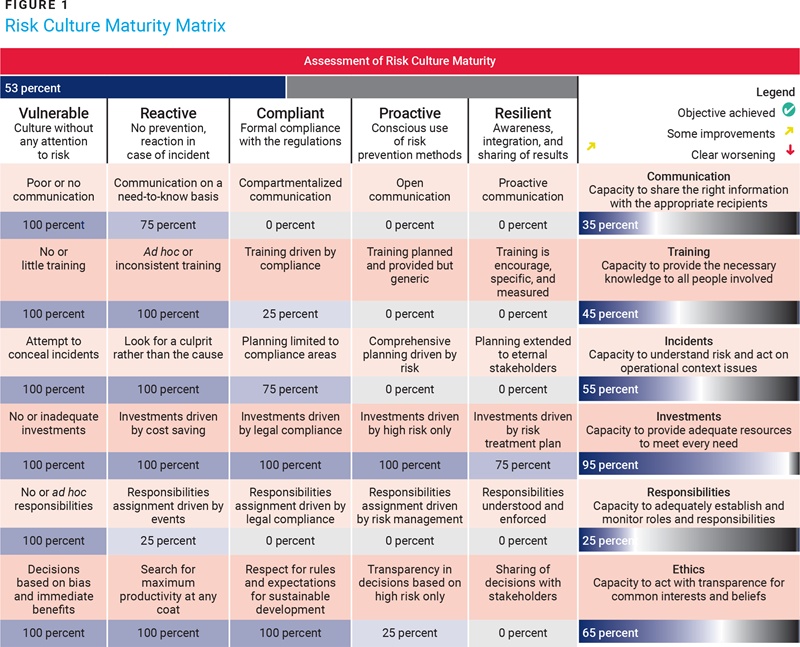
In the example, overall risk culture maturity is assessed to be 53%. For each maturity assessment, it is useful to insert an icon or symbol to highlight the results of the cyclical sequence of assessments. Thus, in each row of the matrix, the icon provides information about the previous assessment. For example, icons could be used to represent achieving or exceeding the established objective (green or blue) and obtaining a result better than the previous one but below the objective (yellow), lower than the previous result (red), or approximately unchanged (orange). The values of the previous assessment and the improvement objective set for each row are stored in hidden columns.
Behavioral Factors in the Assessment of Risk Culture
Determining which areas of the enterprise to include in a risk culture assessment is quite simple. They must be under the direct control of senior management, have a significant impact on the effectiveness of risk management, and be exposed to potentially subjective (i.e., non-risk-based) managerial decisions. These factors could prove to be obstacles to, rather than enablers of, adequate risk management. The following areas and characteristics should be considered.
Communication: Sharing the Right Information with the Appropriate Recipients
Organizational communication should facilitate the sharing of information to manage risk effectively and avoid distrust in management behaviors that might be based on personal beliefs or fear of sharing information. Maturity levels in the communication area can be defined as:
- Vulnerable—The absence of a formal communication system or the presence of unstructured organizational communication that is inadequate to meet needs
- Reactive—The presence of a formal communication system that reacts only to specific requests or events, with circulation limited to what is essential and no real desire to fully share information about risk
- Compliant—An attitude based on fear of the consequences of communication, with a formal approach localized and guided only by the need for regulatory compliance—that is, communicating only when necessary
- Proactive—Full awareness of the importance of managing risk with a holistic vision open to all internal processes involved, providing timely, comprehensive, and reliable communication
- Resilient—Experiencing risk with a full awareness of the consequences, promoting cooperation between processes, and sharing control results, even if the stakeholders are external
Structured communication plays a key role in keeping vulnerability information up to date and reliable among all stakeholders, even those external to the enterprise. Failure to share necessary information with some stakeholders can inhibit the cyclical process of improving the risk management system, until it eventually fails.
Training: Providing the Necessary Information to Everyone Involved
The training of personnel involved in business processes must not be conditioned by managerial behaviors based on the logic of cost reduction. Rather, it must be based on training that is adequate to meet specific rather than general needs. Maturity levels in the training area can be defined as:
- Vulnerable—Lack of a structured training process because training is considered a pure cost
- Reactive—Lack of a structured training process but with the ability to address specific requests or training emergencies
- Compliant—The presence of a structured training process based on the needs of departments and compliance with current regulations
- Proactive—The presence of a structured training process based on the systematic identification of needs, with effective planning and delivery of training but with unmeasured results
- Resilient—The presence of a structured training process that encourages individuals to improve and evaluates the results achieved
Training plays a fundamental role in maintaining the overall efficiency of operations and ensuring the necessary exchange of information among all stakeholders. Knowledge and understanding of the rules of operation and control of the business allow management to correctly allocate resources and operate appropriately, avoiding inefficiencies or errors. Evaluating the actual learning that has taken place and recording the results achieved permit the overall monitoring of the training process.
Incident Management: Understanding Risk and Acting Accordingly
Incident management ensures the operational continuity of business processes and the provision of necessary services. This requires the constant participation of management in the process of identifying critical resources that must be protected and making decisions about the adequacy of the protection measures implemented. Maturity levels in the incident management area can be defined as:
- Vulnerable—An absence of planning and fear of reporting incidents
- Reactive—An absence of planning and a search for the alleged culprit instead of investigating the causes of the incident
- Compliant—Planning is limited to processes subject to regulatory compliance and the formal adoption of methodologies
- Proactive—Cyclical planning for overall business continuity, the central adoption of methodologies, and a search for the causes of incidents that occur
- Resilient—Involvement of all stakeholders, including external ones, in planning, monitoring, reporting, searching for causes, and sharing in the ecosystem
A prompt and effective response to incidents requires a pragmatic approach based on planning and verification of the effectiveness of established measures. Management involvement is essential to ensure coordination, choose the appropriate resources, and make timely decisions based on risk. Planning must ensure control of the time factor in determining and declaring an incident, which is essential for effective response and containment.
Investments: Providing Adequate Resources to Meet Every Need
Investments necessary to obtain the resources identified in the risk treatment plan must not be influenced by subjective managerial behaviors based purely on cost reduction rather than the pursuit of a good compromise between cost and benefit. Maturity levels in the investment area can be defined as:
- Vulnerable—No collection of needs; lack of planning or search for resources
- Reactive—Knowledge of needs and planning for investments, but according to the logic of cost containment
- Compliant—Knowledge of needs and planning for investments, provided they are imposed by compliance with regulations
- Proactive—Knowledge of needs and planning for investments limited to high-risk needs
- Resilient—Knowledge of needs and planning for investments following the needs identified in the risk treatment plan
Investments are essential to effectively implement risk treatment measures. If management perceives these resources as pure costs, the results of the risk assessment must be explained to improve their understanding of the consequences for critical assets. Full awareness of the consequences is required to analyze options and decide on a coherent investment plan.
Acting ethically, transparently, and with respect for the entire ecosystem must not be influenced by managerial behaviors based on fears, prejudices, or individual interests.Responsibilities: Establishing and Monitoring Roles and Responsibilities
Operating methods of business processes must be established. Operational and control roles should be assigned, with defined responsibilities for each role and detailed methods for monitoring processes. Effectiveness with respect to business objectives should be evaluated. Maturity levels in the responsibilities area can be defined as:
- Vulnerable—Lack of adequate organization or a nonformal assignment of responsibilities
- Reactive—Existence of an organizational structure, with formal assignment of responsibilities based on the fear of operational consequences
- Compliant—Existence of an organizational structure, with assignment of responsibilities driven by legal compliance
- Proactive—Presence of an adequate and coherent organization, with assignment of responsibilities driven by risk management
- Resilient—Presence of an adequate and coherent organization, with responsibilities understood, applied, and measured
The assignment of roles and responsibilities must not be influenced by managerial behaviors based solely on the pursuit of high performance or cost containment, or by the fear that formal procedures may slow down operations. The reliability of monitored results and the ability to communicate them in a timely manner are the basis of risk assessment. This requires a managerial structure in which managers are aware of the consequences of their decisions, have the capacity to implement control measures without prejudice, and recognize the importance of taking the appropriate actions.
Ethics: Acting With Transparency for Common Interests and Beliefs
Acting ethically, transparently, and with respect for the entire ecosystem must not be influenced by managerial behaviors based on fears, prejudices, or individual interests. This requires the ability to adopt measures aimed at the common good of the enterprise and the ecosystem in terms of increasing trust in the market. Maturity levels in the ethics area can be defined as:
- Vulnerable—Decisions made with prejudice, seeking immediate individual advantage
- Reactive—Decisions made to obtain maximum productivity at the lowest cost, without considering the stakeholders
- Compliant—Decisions made in compliance with preestablished rules and expectations of future regulations
- Proactive—Decisions made in compliance with transparency but based on the fear of high risk
- Resilient—Risk treatment decisions shared transparently with stakeholders, including vulnerability assessments and incident causes
Ethics plays a fundamental role in creating the conditions that build market and stakeholder trust. It is the basis for improving the value of an enterprise. When significant incidents occur, information about the causes must be shared with all interested parties, even if they are external. Transparency in communication can improve an enterprise’s image in the ecosystem.
Numerical Considerations
Risk culture is assessed by a maturity level expressed through qualitative labels. These labels are associated with numerical values to simplify aggregation, comparison, or prioritization. The choice of the numerical basis influences both the ease of establishing the degree of maturity and the capacity to understand the overall results of an assessment. For example, metrics with a maturity level of 2 (out of 8 levels) or 0.37 (out of a weight of 1.48) or 25% (out of 100%) may represent the same phenomenon but are selected and interpreted differently. A convenient choice is to assign a percentage to the maturity level in the cells of the matrix and define a normalized distribution for the thresholds of passage from one maturity level to another.
The distribution of maturity thresholds allows the emphasis of some levels of maturity compared to others. In practice, low levels of maturity are satisfied easily and quickly, while high ones require greater effort and occur over a longer time. It is useful to be able to choose a distribution of thresholds that is most suitable for the specific situation and highlights the progress of improvement efforts. In the example in figure 2, three different distributions give rise to different assessments of the risk culture starting from the same degree of maturity:
- Linear distribution—All established maturity levels have the same weight and the same evidence in a uniform way.
- Middle (central) emphasis—Low and high levels are compressed, while the trend is clearly highlighted in the center.
- Top (upper) emphasis—Levels up to the middle are compressed, while the trend is highlighted only in the upper part.
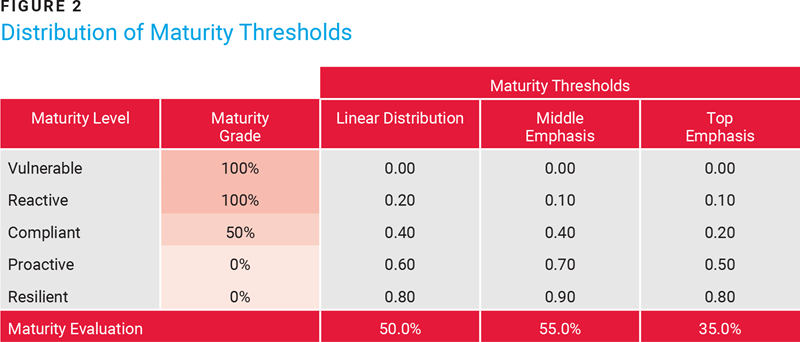
The different overall maturity values are a consequence of the emphasis derived from the choice of the threshold distribution, but this does not lead to inconsistency in the assessments. To analyze the risk culture, an absolute value is not needed; rather, the trend is observed from one assessment to another. For a better understanding of the maturity trend over time, accuracy can be increased by choosing an appropriate distribution of thresholds. This amplifies the values available in the area of interest and highlights the area where corrective interventions are necessary.
Conclusion
Culture encompasses the values, beliefs, knowledge, attitudes, and understanding shared by a group of people with a common purpose. Risk culture expresses the characteristics and particularities of the organizational decisions made to avoid unwanted deviations in the path to achieving business objectives. Concepts introduced in the risk methodology, each of which represents some form of operation, cannot be pure conjecture; they must be measurable elements.
Culture, although not a physical property, must also be measured to make the enterprise aware of the areas that require improvement to achieve resilience. A maturity model is a suitable choice for measurement and must be applied to the components of the risk culture that are considered relevant. It need not provide absolute results; qualitative measurements with respect to a preestablished target are suitable for this purpose. An evaluation carried out according to a comparison of results in temporal sequence allows one to understand the trend of effectiveness of the actions undertaken and therefore identify where to intervene to improve.
Endnotes
1 ISACA®, “Risk Culture,” Glossary
2 International Organization for Standardization (ISO), ISO 31073:2022, Risk Management—Vocabulary, 2022
3 Sbriz, L.; “Yet Another Risk Depiction (YARD),” ISACA® Journal, vol. 3, 2024
4 National Institute of Standards and Technology, Glossary, Computer Security Resource Center (CSRC), USA
5 NIST, Cybersecurity Framework CSF 2.0
6 ISACA, Capability Maturity Model Integration® (CMMI®)
7 ISACA, Certified in Risk and Information Systems Control® (CRISC®) Official Review Manual, 7th Edition, 2021
LUIGI SBRIZ | CISM, CRISC, CDPSE, ISO/IEC 27001 LA, ITIL V4, NIST CSF, TISAX AL3, UNI 11697:2017 DPO
Is a lead auditor, trainer, and senior consultant on risk management, cybersecurity, and privacy. He is also a member of several international associations on cybersecurity, risk, and privacy. Sbriz has been responsible for risk monitoring at a multinational automotive company for more than seven years. Previously he was responsible for ICT services and resources management in the Asia-Pacific region (China, Japan, and Malaysia) after serving as worldwide information security officer for more than seven years. He developed an original methodology for risk monitoring, integrating operational risk analysis tools, conducting control maturity assessments, and executing a risk-based internal audit process. Additionally, he designed an OSINT-based cybermonitoring tool and is proposing a digital identity authentication standard. He can be reached on LinkedIn (https://www.linkedin.com/in/luigisbriz).