Unified secure access service edge (SASE) as a service1 integrates networking and security mechanisms into a single, unified platform. A cloud-native architecture, it combines key technologies such as zero trust network access (ZTNA), secure web gateways (SWGs), firewall as a service (FWaaS), cloud access security brokers (CASBs), and other security features to provide secure, seamless access to applications and data across distributed environments. By delivering these capabilities through a unified service, SASE reduces complexity, enhances scalability, and improves visibility across hybrid and multi-cloud architectures. It ensures consistent security policies and real-time threat protection, regardless of user location or device. Unified SASE as a service empowers organizations to adapt quickly to dynamic needs, streamline operations, and enhance their overall cybersecurity posture while supporting modern, flexible workforces.
In today’s rapidly evolving threat landscape, organizations require agile security incident response (ASIR) to manage and mitigate the impact of cyberthreats effectively. ASIR is a dynamic approach to managing and mitigating cybersecurity incidents. It applies agile methodologies often used in software development to improve incident response process effectiveness, speed, and adaptability. ASIR enables organizations to trigger rapid and effective responses, demonstrating a commitment to security and minimizing the potential for reputational damage. This helps maintain customer trust and build reputation.
There are several powerful ways that unified SASE as a service can enable ASIR:
- It significantly enhances the scalable cloud-native incident response. Consider a hybrid workforce scenario where employees access enterprise resources from multiple locations. If anomalous behavior triggers an incident, SASE dynamically enforces secure access controls and policies based on user identity and device posture, automatically restricting access to the user account.
- It efficiently automates incident containment. For example, suppose malicious code is running on an endpoint. In that case, a unified SASE platform harnessing the power of artificial intelligence (AI)/machine learning (ML)-powered anomaly detection can swiftly and automatically quarantine the affected device, block malicious traffic, and enforce zero-trust access policies, stopping the spread before security teams intervene.
- It dramatically reduces response time with automation as teams respond to threats at lightning speed by leveraging security orchestration and automated playbooks. For example, if a phishing attack is detected, automated workflows can block malicious domains, alert affected users, and initiate email filtering rules to prevent further compromise.
- It provides real-time unified visibility, enabling security teams to gain centralized telemetry across all cloud, network, and endpoint environments. This ensures that no blind spots are observed during an investigation. For instance, if an attack originates from a cloud workload, the security team can track its full attack path in real time and mitigate it before it affects critical systems.
By following agile delivery principles, unified SASE as a service ensures that organizations can respond to security incidents quickly, precisely, and with minimal disruption.
Understanding Challenges and the Need for ASIR
ASIR is crucial in today’s dynamic and complex cyberenvironment. Agile practices enhance an organization's ability to manage and mitigate security incidents effectively by enabling rapid adaptation to emerging threats,2 optimizing operational efficiency, and maintaining customer trust. The need for agility in incident response is driven by the significant rise in the complexity of cyberthreats,3 technological advancements, regulatory demands, and the necessity to protect critical organizational operations and reputation. It is important to understand the reasons why ASIR is the need of the hour:
- Organizations operate with distributed and global networks to run operations worldwide, which can complicate incident response efforts. ASIR facilitates a coordinated and effective response across diverse geographic locations and network segments. For example, organizations face security challenges due to the rise of remote and hybrid work environments. ASIR ensures that response strategies are effective across various remote and on-site work scenarios.
- ASIR allows organizations to quickly contain and mitigate security incidents, reducing the risk of extended downtime and operational disruption. It helps optimize resource use by enabling organizations to focus on the most critical incidents and deploy appropriate resources efficiently to minimize response time.
- Due to the resurgence of dynamic IT environments, organizations opt for new technologies and deploy them quickly, resulting in more complex IT environments. ASIR enables organizations to manage the security implications of these technological changes and ensure that security measures keep pace with innovations and protect the newly deployed technologies.
- There has been an exponential rise in sophisticated internet attacks. ASIR enables a focused approach to these complex threats by prioritizing and swiftly addressing incidents, minimizing potential damage and disruption.
- ASIR leverages threat intelligence and guides actions based on mature response strategies4 by harnessing the latest data and trends. ASIR enables organizations to continuously refine and enhance their incident response processes based on lessons learned from previous incidents. As a result, organizations can respond to data breaches promptly and provide required notifications within mandated timeframes. Audit preparedness is essential for demonstrating adherence to security standards and regulatory requirements.
Dissecting the Key Components of ASIR
There are five key components of ASIR, as presented in figure 1.
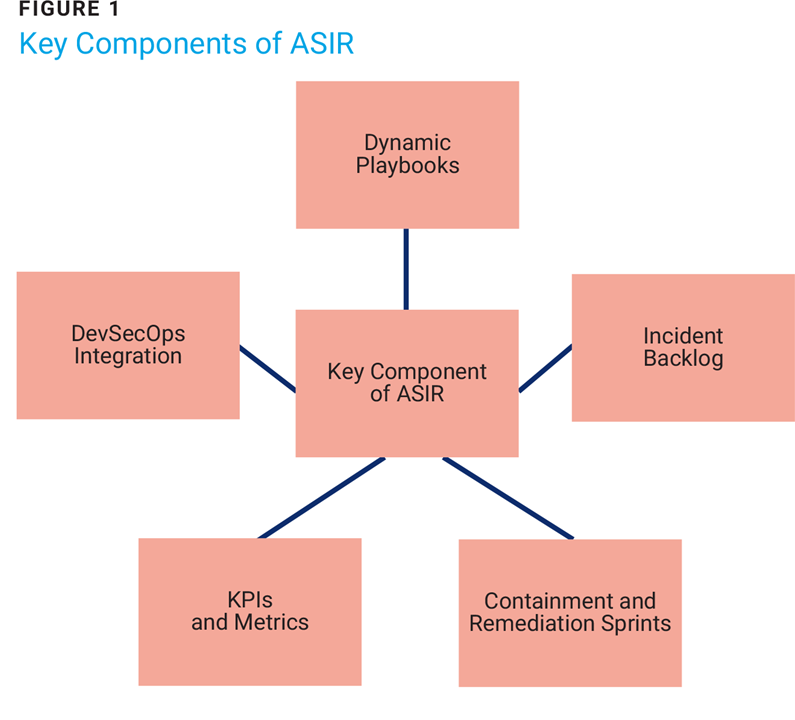
Dynamic Playbooks
Dynamic playbooks are adaptive, real-time response frameworks that address evolving security incidents. Unlike static playbooks, which follow predefined steps, dynamic playbooks5 leverage contextual data, real-time threat intelligence, feedback loops, and automation to adjust responses as incidents unfold. For example, integrating ML models to detect anomalies can trigger containment or escalation procedures dynamically. This approach is efficient in agile environments where flexibility is critical. By integrating dynamic playbooks into incident response, teams can deploy modular workflows to rapidly evaluate the scope of a threat, adapt to unique attack patterns, prioritize actions, reduce response time, and allocate resources efficiently to minimize damage. Dynamic playbooks also enhance collaboration across teams by providing clear, role-based guidance for each stage of an incident. With proper implementation, dynamic playbooks streamline incident response and ensure compliance with organizational and regulatory standards in a dynamic threat landscape.
Incident Backlog
An incident backlog is a structured repository of unresolved or previously addressed security incidents that require follow-up, analysis, or remediation. Inspired by agile principles, the backlog categorizes incidents based on priority, severity, and complexity, enabling teams to tackle the most critical issues first. It is a single source of truth for security teams, promoting transparency and accountability. This systematic approach ensures that no incident is overlooked while allowing for strategic planning of resources and efforts. Organizations can better track recurring vulnerabilities, identify trends, and allocate resources for long-term improvements by maintaining an incident backlog. Integrating the backlog into agile workflows ensures that addressing security incidents becomes part of the development cadence, fostering a proactive and iterative approach to strengthening the organization’s overall security posture.
Containment and Remediation Sprints
These sprints are focused, time-boxed efforts within an agile framework to address security incidents effectively. They prioritize immediate containment to mitigate ongoing threats, followed by detailed remediation to eliminate vulnerabilities and restore systems to a secure state. Organizations can balance rapid action with methodical resolution by dedicating specific sprint cycles to incident response, preventing disruptions to overall project timelines. Leveraging agile principles, teams can break down complex tasks into manageable components, fostering collaboration and accountability. Retrospectives at the end of each sprint provide insights into what worked and what did not, feeding into a continuous improvement cycle. Containment and remediation sprints thus bridge the gap between immediate incident response and long-term security resilience.
KPIs and Metrics6
Key performance indicators (KPIs) and metrics are nonnegotiable for measuring the effectiveness of an ASIR strategy. They provide quantitative insights into the performance of response teams and an organization's overall security posture. Common KPIs include mean time to detect (MTTD), mean time to respond (MTTR), and the number of incidents resolved per sprint. Tracking these metrics allows organizations to identify bottlenecks in the incident response process and allocate resources more effectively. Metrics also support decision making by providing data-driven insights into incident trends and vulnerabilities. For example, tracking the percentage of recurring incidents can highlight systemic issues, while the volume of incidents closed versus opened indicates the efficiency of response efforts. When integrated into dashboards accessible to stakeholders, these metrics promote team transparency and alignment. Robust KPIs and metrics enable organizations to continuously refine their incident response strategies and demonstrate the value of security efforts to leadership.
DevSecOps Integration
Integrating DevSecOps into ASIR ensures that security becomes a shared responsibility across development, security, and operations teams. This approach embeds security into every software development life cycle (SDLC) phase, facilitating faster detection and resolution of vulnerabilities. By automating security checks and incorporating tools such as static application security testing (SAST) and dynamic application security testing (DAST), DevSecOps enables teams to address issues before they escalate into incidents. Continuous feedback loops between developers, security engineers, and operations teams enhance the organization’s ability to detect and mitigate threats in real time. Leveraging shared metrics such as deployment frequency and incident closure rates ensures that security objectives align with agile goals. By uniting DevSecOps principles with incident response, organizations can achieve a more resilient and proactive security posture.
Once the key components of ASIR are understood, it is essential to understand how to use unified SASE as a service to enable ASIR.
Enabling ASIR With Unified SASE as a Service
Unified SASE as a service is a transformative enabler for ASIR, combining security and network capabilities into a single, cloud-delivered solution. It ensures rapid detection, containment, and remediation of incidents across decentralized environments. Its centralized management and automation capabilities streamline incident response workflows, reducing response times and enhancing team coordination. By providing consistent security policies and scalable infrastructure, unified SASE supports ASIR’s need for flexibility and real-time adaptability, empowering organizations to stay resilient against evolving threats while maintaining organizational operations without interruption. Figure 2 highlights how unified SASE as a service empowers organizations to take advantage of ASIR.
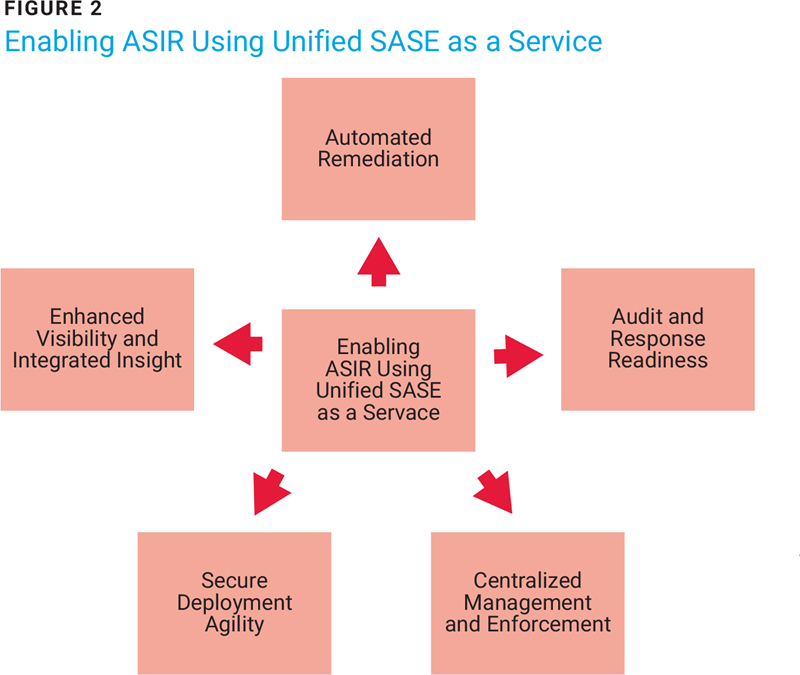
Unified SASE as a service lends itself to ASIR due to several factors:
- Automated remediation—Unified SASE as a service allows automated remediation to reduce response times significantly. Traditional security approaches often rely on manual intervention, which is prone to errors, especially during high-pressure situations. SASE, however, automates critical response actions such as isolating compromised devices, blocking malicious traffic, and applying security patches before they can spread and cause more damage. This minimizes the exposure window and ensures consistent application of remediation steps across the network. Overall, it helps reduce MTTD and MTTR. In addition, with the built-in security orchestration, automation, and response (SOAR)-like capabilities, the SASE platform automates detection, triage, and remediation workflows.
- Audit and response readiness—Unified SASE as a service provides detailed logs and reports essential for incident investigation and compliance. These audit trails can be used to better understand a security incident's scope and impact. With unified SASE as a service:
- Logs are consolidated into a centralized repository, providing information about all network and security events including user activities, access requests, policy changes, and threat detections. This information is used to investigate the root causes of security incidents. Investigators can trace the sequence of potential events, dissect the source of the breach, and understand the impact of the incident.
- Immutable and tamper-proof logs against unauthorized modifications are provided to ensure the integrity and trustworthiness of the audit trails for compliance and forensic analysis.
- Historical data is retained that can be used to analyze trends and patterns over time. This perspective is valuable for identifying persistent threats and improving security strategies.
With unified SASE as a service, the inherent cloud-native architecture ensures rapid scaling during incident occurrence to handle traffic as required.
- Centralized management and enforcement—A single management interface for all security and networking functions streamlines the incident response process, making it easier for the networking and security teams to coordinate their efforts. Additionally, the centralized management and unified visibility provided by SASE ensure that all security incidents and remediation efforts are logged and monitored, facilitating better reporting, compliance, and audit readiness. Overall, unified SASE as a service integrates network and security monitoring into one platform, reducing silos to provide a single-pane-of-glass view across cloud, on-premises, and remote environments.
- Secure deployment agility—Unified SASE as a service flexibility enables quick deployment of security updates and patches uniformly across the entire network infrastructure, ensuring rapid adaptation to emerging threats. Deployment agility for post-incident response is essential for building and maintaining a robust security posture and ensuring that organizations can quickly adapt, learn, and recover from security incidents. Organizations can rapidly implement lessons learned, update policies, and enhance their overall security measures by leveraging automation, continuous improvement, scalability, and integration of security and networking functions. Secure deployment agility not only helps mitigate the impact of future incidents but also ensures compliance, improves strategic and operational efficiency, and fosters a culture of proactive security management.
- Enhanced visibility and integrated insights—Unified SASE as a service provides intuitive insights into network and security activities. It can quickly provide an understanding of the state of the network, inherent risk, active threats, and anomalies using dashboards and visualization tools. Integrated threat intelligence enhances the quality of logs and reports with correlation and context about the latest threats. As a result, organizations can respond to emerging threats efficiently and adjust their security posture accordingly. Unified SASE as a service combines capabilities such as CASB, SWG, FWaaS, and ZTNA to streamline incident response by eliminating the need for disparate tools. Further, it enables continuous updates on emerging threats for rigorous detection and adaptation of defenses by performing correlation of global and local intelligence streams for a tailored response.
Conclusion
Unified SASE provides a single platform that handles detection, containment, and recovery, reducing tool sprawl and improving team efficiency. By leveraging automation, SASE minimizes manual intervention, accelerates incident response, and enhances containment and remediation efforts. The SASE platform enables unified telemetry from all endpoints, networks, and cloud services to ensure no blind spots during an investigation. Unified SASE integrates AI/ML-driven proactive anomaly detection, significantly reducing the time attackers remain undetected.
ASIR benefits significantly from unified SASE as a service’s ability to adapt to rapidly changing attack vectors, ensuring swift containment and remediation. With SASE's global presence and real-time data insights, organizations can prioritize incidents effectively, accelerate response times, and maintain consistent security postures, even in decentralized or hybrid work environments. Ultimately, combining agile methods with unified SASE as a service empowers organizations to mitigate risk proactively, maintain business continuity, and adapt seamlessly to evolving threats.
Endnotes
1 Aryaka, “What is SASE and Unified SASE as a Service?”
2 Verizon, 2024 Data Breach Investigations Report, 2024
3 Jones, H.; “Cyber Threats And The Growing Complexity Of Cybersecurity And IT Infrastructure Management,” Forbes, 11 July 2024
4 Statsig, “Effective Incident Response Planning Strategies,” 5 August 2024
5 Microsoft, “Microsoft Incident Response Playbooks,” 24 October 2024
6 Wilkins, L.; KPIs for CSIRTs, Cisco, 2024
ADITYA K SOOD
Is the vice president of security engineering and AI strategy at Aryaka. With 17 years of experience in cybersecurity, he has worked for companies such as F5, Symantec, Bluecoat, and KPMG. Sood authored Combating Cyberattacks Targeting the AI Ecosystem and Empirical Cloud Security and Targeted Cyber Attacks and frequently speaks at industry-leading security conferences.