

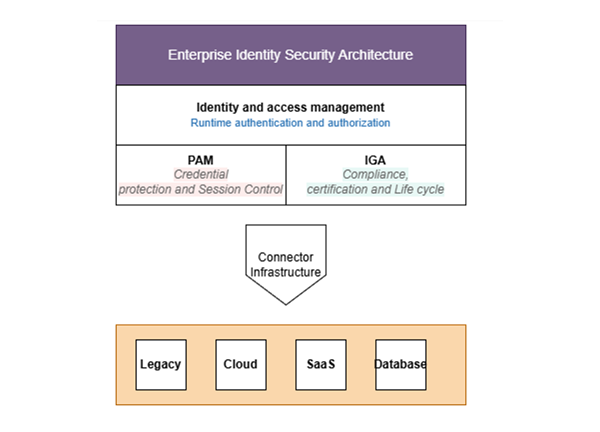
Rapidly evolving IT frameworks such as identity and access management (IAM), identity governance and administration (IGA), and privileged access management (PAM) form the foundational pillars of managing user identities and access across an organization. IAM provides runtime authentication and authorization tools (e.g., single sign on [SSO], multifactor authentication [MFA]) as well as federation protocols (e.g., security assertion markup language (SAML), OpenID Connect (OIDC), and OAuth 2.0), directory services, and session management.1 PAM focuses on high-risk admin accounts, securing credentials in a vault with automated rotation, just-in-time privilege elevation, session recording, and secrets management.2 With the IGA framework, organizations can accomplish periodic access review, detailed compliance reporting, and provision workflow automation, enhancing efficiency and security across teams.3 Combining these 3 environments reduces security blind spots and prevents unauthorized access. Figure 1 illustrates a simplified enterprise identity security architecture. The diagram emphasizes the connector infrastructure as the critical dependency layer beneath IAM, PAM, and IGA. This layer enables integration with the heterogeneous enterprise ecosystem, including legacy systems, cloud platforms, SaaS applications, and databases.
Figure 1—Enterprise Identity Security Architecture: IAM, IGA, and PAM Integration
The benefits of IGA platforms rely on the assumption that the standard, out-of-the-box connector that comes with a commercial off the shelf (COTS) IGA product can be plugged in to any system.4 However, this assumption rarely holds true in real-world enterprise environments. Many organizations today depend on a combination of mainframes, specialized software as a service (SaaS) tools, and custom applications designed years ago, many of which do not offer compatibility with standard connectors.5 This results in governance black holes where system access is manually granted. In such situations, organizations often face issues such as orphaned accounts, excessive or inappropriate privileges, missing or incomplete audit trails, and delayed access revocation after employee role changes or termination.6 These issues can all result in critical security vulnerabilities.7
The path forward starts with shifting the mindset about organizational COTS IGA platforms. Rather than embracing them as a complete, ready-to-deploy solution, it is crucial to approach such platforms as a foundation to build on. Furthermore, by using software development kits (SDKs), organizations can build custom connectors and accomplish the end-to-end automation that state-of-the-art identity governance requires.8
Where COTS Solutions Fall Short
For common commercial applications, such as Active Directory, Office 365, and Salesforce, off-the-shelf connectors are relatively effective because these platforms provide well-documented application programming interfaces (APIs), stable identity schemas, and standardized provisioning interfaces, allowing for seamless enterprise control.9 However, COTS performance degrades in certain environments, including:
- Legacy systems—Domestic applications that were designed years ago and have no representational state transfer (REST) API. These systems only rely on custom authentication methods.
- Niche SaaS applications—Department-level subscriptions or newer, evolving tools may not yet be part of the IGA vendor’s roadmap.
- Specialized enterprise systems—Proprietary software is used in domains such as research, manufacturing, and healthcare, and works independent of the conventional IT stack.
- Complex enterprise resource planning/human resources(ERP/HR) systems—Despite critical ERP/HR platforms being supported, accessing their layered, complex privileges requires custom logic.
Due to the lack of prebuilt connectors, organizations have historically had to depend on manual, spreadsheet-heavy processes, resulting in weakened governance.10 Designing a custom connector is one of several approaches organizations can take to integrate unsupported systems and bring reliable governance and control into an automation workflow.
The Composition of a Custom Connector
Custom connectors11 are not a simple API call—they are a complex software component that behaves similar to a 2-way translator between the target system and the IGA platform. When a custom connector is designed to utilize the target system’s SDK, several key controls are implemented, including:12
- Account administration—Create, activate, and deactivate accounts of users on the target system.
- Privilege discovery—Read and understand the roles, groups, and access rights on the target system (this is critical because it requires a detailed understanding of the application security structure).
- Access provisioning—Grant/deny access permissions for users, imposing the decisions conducted by the IGA platform.
- Password handling—Manage password synchronization and resets, provided it is supported and safe. Password management should only be enabled when the target system supports secure API-based password updates and encrypted communication. Legacy systems, which require plaintext password handling, introduce significant security risk and should be avoided, consistent with guidance from the National Institute of Standards and Technology (NIST) Digital Identity Guidelines.13
- Reconciliation—Conduct frequent health checks to ensure that the IGA platform access record matches the target system, correcting any issues identified.
While these controls are essential for effective identity governance, implementing them within custom connectors requires significant engineering effort and architectural planning. Developing connectors that accurately interpret application security models, support reliable provisioning, and maintain reconciliation integrity often involves deep knowledge of the target system’s APIs or SDKs. As a result, organizations must carefully evaluate the cost and operational implications of connector development—an investment that, when executed strategically, can significantly improve governance visibility, reduce manual access management, and strengthen enterprise security posture.
A Real-World Example: Building a Custom Connector for Cloud Identities
Imagine a rapidly growing tech organization that relies on a popular IGA platform for identity governance. At the same time, the organization’s engineering teams also rely heavily on a specific cloud provider’s managed identity service (e.g., Amazon Web Services [AWS] IAM, Azure Managed Identities). The out-of-the-box connector for such services comes as a premium add-on with costly licensing expenses, burdening the entire budget. Apart from that, the standard connector is designed for general purposes and fails to meet enterprise-specific challenges such as handling thousands of short-lived, project-based service accounts effectively.14
The Solution: A Lightweight, Purpose-Built Custom Connector
Instead of investing in expensive broad commercial connectors, the tech organization utilized its chosen IGA platform to design a custom connector tailored to specific requirements, including:
- Public APIs—The target cloud provider provided the organization with a detailed, well-documented public API for its identity service. Utilizing the API along with the IGA SDK’s base connector framework, the organization’s security team led a streamlined, lightweight integration.15
- Focused scope for cost and efficiency—The organization’s custom connector is designed specifically for managing access to cloud resources that the organization’s engineering teams require, primarily service accounts and the roles linked to them. This approach circumvents the need to grant access to the entire cloud resource catalog as provided by a commercial connector, making implementation simpler to design, improving operational speed, and proving more cost efficient.16
The connector was also designed to facilitate several tasks, including:
- Aggregation—At a predefined frequency, preferably daily, the connector reads the details of all service accounts and their associated roles from the cloud project and ensures that data is retrieved as per a predefined schema for governance.
- Certification—To improve security posture, the connector inputs the aggregated data into the organization’s IGA platform. Project owners then use this data to validate access for cloud identities.
- Provisioning—The connector can create, modify, and revoke identity and access directly in the target system based on policies maintained in IGA platform. To achieve state-of-the-art automation, connectors rely on privileged service accounts to perform administrative actions in the target system. This makes identity management smoother and more reliable.17
This approach ensured that the organization’s engineering teams were able to mitigate costly and recurrent license fees associated with commercial connectors. It offered them the governance capabilities critical to assuring compliance and security without the burden of unwanted features.
Not only was the custom solution optimal in terms of cost, but it also grants flexibility in the longer term, as it allows internal teams to adopt controls that align with the transformation of their organization’s cloud governance policies, all without the need to wait for vendor updates.18
Best Practices for Sustainable Custom Connector Development
While initial connector development is complex, sustaining and evolving it over time often proves to be the greater challenge. For smoother operations and long-term success, it is imperative to:
- Value the connector as a product. Custom connectors are frequently developed as ad hoc integrations, and they often lack proper life cycle management, testing, and security controls.19 Organizations should treat custom connectors as their own product because they form a critical infrastructure component of an organization’s governance platform. They require effective version control, continuous integration/continuous delivery (CI/CD) pipelines, and devoted maintenance guidance for long-term sustainability.20
- Prioritize error handling and logging for operational resiliency. Connector-operated environments are often unpredictable and dynamic. To mitigate risk, implement robust logging practices and retry mechanisms, which help address challenges such as invalid credentials and network timeouts. Ensure that errors are never silently ignored and are properly logged to maintain operational transparency.21
- Accept idempotency. Make sure that the logic of provisioning is designed in such a manner that if a command is executed multiple times, it offers the same output as running it once. This method minimizes duplicate access, resulting in a more predictable system.22
- Prepare for the target system's evolution. Due to the evolving nature of application APIs, it is necessary to design the connector in such a way that the API-based logic is separated from governance rules. This will make sure that future version upgrades are controlled and operations are not disrupted.23
- Treat security as a priority. Custom connectors often require credentials with excessive access. Ensure that these credentials are placed within the IGA platform's secure store or enterprise vault and enforce least privilege access on the target system.24
- Implement an integration and control framework to manage custom connectors efficiently. As the digital landscape continues to change, cloud-native capabilities, SaaS applications, and API-based microservices will be built—and they will require critical governance controls. As the inventory of in-house custom connectors increases over time, connectors must be built based on a configuration-based template design pattern rather than a one-off development exercise for ease of development and ongoing maintenance.25
Conclusion
Modern COTS IGA platforms are about more than their ability to carry out governance capabilities instantly out of the box. What truly matters is how they can be extended to address the complicated, interconnected realities of organizations across industries. This is what will empower engineering teams to deal more efficiently with ever-evolving challenges. Custom connectors offer end-to-end automation and provide IT teams with the tools to adapt to continuously changing business needs. By employing such an approach, organizations can modernize their IGA platform from a simple monitoring tool to one that can effectively govern critical systems. This ultimately enhances the organization's security posture and operational efficiency. The implementation of custom connectors helps organizations ensure that every application, from a new SaaS tool to the most critical legacy application, is tightly managed, visible, and compliant with regulatory and security requirements. Building custom connectors not only addresses governance issues but also meaningfully prepares organizations for the myriad risk, issues, and challenges that have not yet arrived.
Endnotes
1 Cameron, A.; Williamson, G.; "Introduction to IAM Architecture (v2)," IDPro Body of Knowledge, vol. 1, iss. 6, 2020
2 Koot, A.; "Introduction to Privileged Access Management (v2)," IDPro Body of Knowledge, vol. 1, iss. 13, 2024
3 Cameron, et al., “Introduction to IAM Architecture”
4 Thiemann, T.; “Identity Governance and Administration, App Proliferation, and the App Integration Chasm,” Dark Reading, 14 November 2025
5 Haines, K.; “Navigating the App Integration Chasm in Identity Governance,” Security Curated, 17 November 2025
6 National Institute of Standards and Technology (NIST), SP 800-53 Rev.5, Security and Privacy Controls for Information Systems and Organizations, USA, September 2020
7 Productiv, “12 Saas Statistics That Every IT Manager Should See in 2024,” 30 March 2024
8 Oracle, “Fusion Middleware Developer's Guide for Oracle Identity Manager”
9 Kovacevic, I.; Rankovic, T.; et al.; “Token-based Identity Management in the Distributed Cloud,” arvix, 2024
10 Peck, T.; “Think IGA Is Challenging? You’re Not Alone,” Cyberark, 29 October 2025
11 The Functional BA, “What is a Custom Connector,” 26 January 2025
12 Wairagade, A.; "IGA Connectors: The Bridge Between Policy and Execution," 28 October 2025
13 NIST, "Cybersecurity and Privacy Reference Tool,” USA, 2022
14 CyberArk, “What is Modern Identity Governance and Administration?”
15 NIST, Special Publication 800-228, Guidelines for API Protection for Cloud-Native Systems, USA, June 2025; Hunt, P.; Grizzle, K.; et al.; “System for Cross-Domain Identity Management (SCIM): Protocol,” Internet Engineering Task Force
16 ZigiWave, "Custom vs. Pre-Built Connectors for Enterprise Application Integration"
17 Wairagade, “IGA Connectors”
18 Smouts, K.; “Overcoming the Challenges of Legacy Identity Governance and Administration (IGA),” Zygon, 16 July 2025
19 OWASP, “Software Assurance Maturity Model (SAMM)”
20 Cameron, et al., “Introduction to IAM Architecture”
21 Refgrow, “8 Essential Software Integration Best Practices for 2025,” 25 June 2025
22 RFC 7644 (SCIM Protocol): SCIM operations are designed to be idempotent. The PUT operation replaces the complete resource, ensuring a consistent state. See: Hunt, Grizzle,“System for Cross-Domain Identity”
23 Virlan, A.; “Building a Modern SaaS Connectivity Platform,” Medium, 9 May 2023
24 Amazon Web Services (AWS), “Security Best Practices in IAM”
25 Aquino, J.; Goodwin, M.; “Low-Code Integration, Defined,” IBM, 3 February 2026
Anant Wairagade
Is a senior cybersecurity engineer with more than 20 years of experience in software and security engineering, aiding IT organizations with digital transformation and helping them become more secure. In his career of more than 2 decades, Wairagade has worked for various financial services enterprises, where he led the design and development of several successful products in the security, finance, and financial CRM domain. At the beginning of his career, Wairagade worked as a technology consultant for major financial services enterprises and banks. Wairagade is a thought leader in enterprise integrations solutions. He is an expert in application programming interface (API)-based data connector development, Kafka, and messaging middleware. Wairagade is also an active member of several Industry open standard communities.
